资讯类
Win10用户安装Meltdown/Spectre漏洞的安全更新KB4056892后无法启动系统
许多用户在微软社区(answers.microsoft.com)下抱怨说,在安装了Windows对 Meltdown/Spectre漏洞的安全更新KB4056892之后,搭载AMD速龙的PC就无法启动了,无法进入安全模式,只能看到Windows启动logo。多次启动失败之后,就开始回滚,然后显示错误0x800f0845 。不幸的是,在没有修改gpedit(组策略)的情况下,很难禁用掉自动更新,于是就开始不停地安装更新然后回滚。一些用户称即便重装Windows10也不能解决。
详情见:
https://www.reddit.com/r/sysadmin/comments/7ode4s/problems_with_windows_7_quality_rollup_kb4056894/
苹果为Spectre漏洞发布iOS和macOS更新
(苹果发布了macOS High Sierra 10.13.2补充更新,iOS 11.2.2和Safari 11.0.2,包含对Spectre漏洞的缓解措施。此前在2017年12月发布了iOS 11.2,macOS 10.13.2和tvOS 11.2,以修复Meltdown漏洞(CVE-2017-5753))
https://www.bleepingcomputer.com/news/apple/apple-releases-security-updates-for-spectre-cpu-flaw/
https://support.apple.com/en-us/HT208397
https://support.apple.com/en-us/HT208401
WPA3 WiFi认证协议的第一份正式草案将在今年晚些时候发布
腾讯安全玄武实验室发布的对Spectre漏洞的在线监测工具
http://xlab.tencent.com/special/spectre/spectre_check.html
2017 Black Hat Europe大会回顾
技术类
Spectre CVE-2017-5753 PoC for Android/ARM64
https://github.com/V-E-O/PoC/blob/master/CVE-2017-5753/source.c
mcafee发布2018年威胁预测
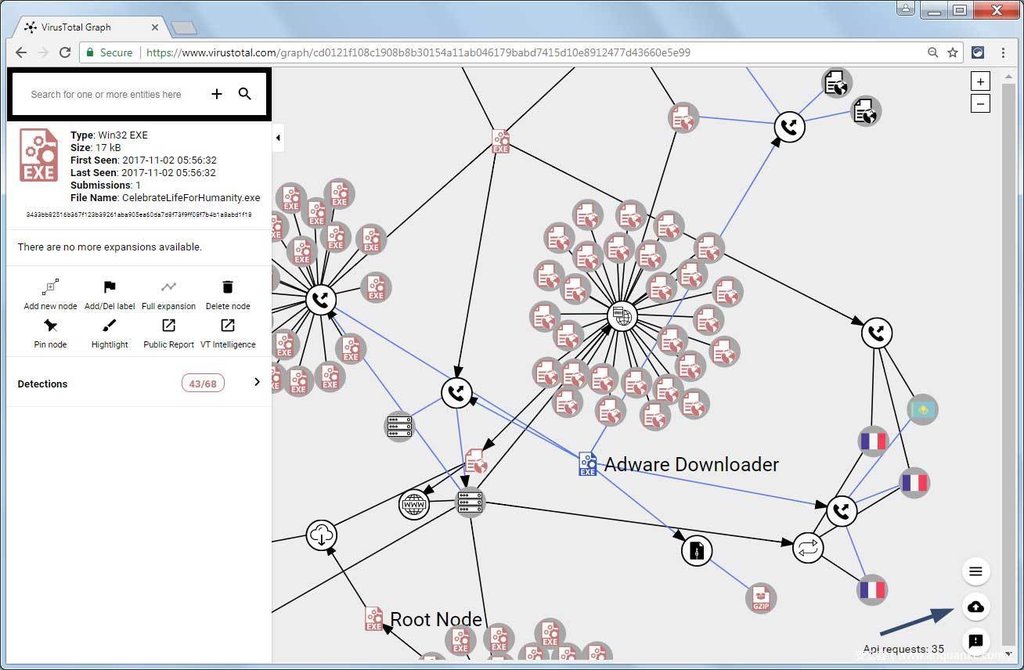
VirusTotal Graph增加新特性,查看各文件的相关性更容易
mcafee对瞄准平昌奥运会的恶意文件的分析
https://securingtomorrow.mcafee.com/mcafee-labs/malicious-document-targets-pyeongchang-olympics/
使用硬件性能计数器检测Spectre & Meltdown漏洞
Spectre & Meltdown漏洞检测工具
https://github.com/speed47/spectre-meltdown-checker
看我如何利用D-Link 815N
https://cr0n1c.wordpress.com/2018/01/08/exploiting-cheap-labor/
https://github.com/Cr0n1c/dlink_815_shell_poc/blob/master/dlink_auth_rce
Oracle WebLogic <10.3.6 wls-wsat组件反序列化远程命令执行
https://cxsecurity.com/issue/WLB-2018010082
Cisco Talos团队对Meltdown and Spectre漏洞的解读
http://blog.talosintelligence.com/2018/01/meltdown-and-spectre.html
FiberHome LM53Q1多个漏洞(CVE-2017-16885, CVE-2017-16886, CVE-2017-16887)的exploit
https://www.exploit-db.com/exploits/43460/







发表评论
您还未登录,请先登录。
登录