资讯类
BH欧洲会议中安全研究员提出了新的攻击方式:Process Doppelgänging,目前该攻击可针对所有Windows版本
维基解密公布的内容正在被美国当局进行深入调查
https://mobile.nytimes.com/reuters/2017/12/07/world/europe/07reuters-usa-trump-russia-wikileaks.html
安全漏洞导致主流银行App面临中间人攻击风险
https://thehackernews.com/2017/12/mitm-ssl-pinning-hostname.html
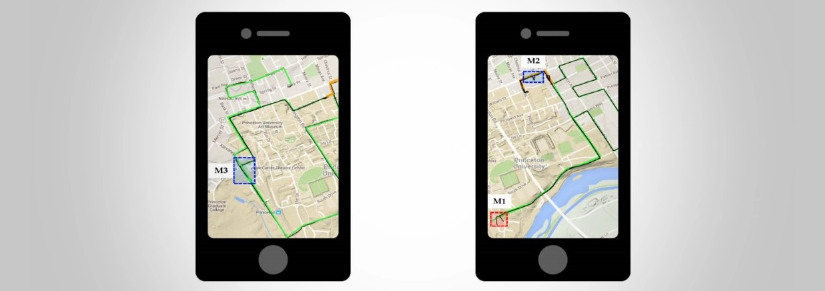
安全研究人员发现手机在GPS关闭时也有办法追踪用户位置
https://www.bleepingcomputer.com/news/security/apps-can-track-users-even-when-gps-is-turned-off/
技术类
网络犯罪成本解析
https://www.recordedfuture.com/cyber-operations-cost/
APT34利用CVE-2017-11882针对中东进行攻击
https://www.fireeye.com/blog/threat-research/2017/12/targeted-attack-in-middle-east-by-apt34.html
Sysinternals Sysmon可疑活动指南
https://blogs.technet.microsoft.com/motiba/2017/12/07/sysinternals-sysmon-suspicious-activity-guide/
DDE的新替代:利用Excel的新攻击方式
https://www.lastline.com/labsblog/when-scriptlets-attack-excels-alternative-to-dde-code-execution/
CTF365 Blitz Writeup
https://medium.com/@thel3l/ctf365-blitz-ctf-writeup-c97f0bc43e6b
无需主机名验证的半自动Pinning检测
http://www.cs.bham.ac.uk/~garciaf/publications/spinner.pdf
BH17议题:如何攻击关机的计算机或在Intel管理引擎运行未签名代码
微软关于CVE-2017-11937漏洞通告
https://portal.msrc.microsoft.com/en-US/security-guidance/advisory/CVE-2017-11937
Trape:互联网追踪与反追踪工具
https://github.com/boxug/trape
新的安卓漏洞可让攻击者在不影响签名的情况下修改App
Web应用中实现定时攻击以破解密码
http://blog.ichikaway.com/entry/2017/12/08/091349
通过不同密码分析方式解码空调校验和
http://www.righto.com/2017/12/decoding-air-conditioner-controls.html
深入解析IOSurface
https://siguza.github.io/v0rtex/
WebAccess webvrpcs ViewDll1基于栈的缓冲区溢出RCE漏洞
https://github.com/rapid7/metasploit-framework/pull/9286
Apache Thrift渗透测试
https://www.mdsec.co.uk/2017/12/penetration-testing-apache-thrift-applications/








发表评论
您还未登录,请先登录。
登录